B

Networking Fundamentals Quiz
Test your knowledge on networking fundamentals with this comprehensive quiz designed for networking enthusiasts and professionals alike. Dive into various topics including routing protocols, VLANs, IP addressing, and more.
With 49 challenging questions, you can:
- Assess your current networking knowledge
- Identify areas for improvement
- Prepare for networking certifications

1 Refer to the exhibit. Host A has sent a packet to host B. What will be the source MAC and IP addresses on the packet when it arrives at host B?
Source MAC: 00E0.FE91.7799 Source IP: 192.168.1.1
Source MAC: 00E0.FE10.17A3 Source IP: 10.1.1.10
Source MAC: 00E0.FE91.7799 Source IP: 10.1.1.10
Source MAC: 00E0.FE10.17A3 Source IP: 192.168.1.1
Source MAC: 00E0.FE91.7799 Source IP: 10.1.1.1
2 What is the effect of configuring the ipv6 unicast-routing command on a router?
To assign the router to the all-nodes multicast group
To enable the router as an IPv6 router
To permit only unicast packets on the router
To prevent the router from joining the all-routers multicast group
3 What is a characteristic of a static route that creates a gateway of last resort?
It backs up a route already discovered by a dynamic routing protocol.
It uses a single network address to send multiple static routes to one destination address.
It identifies the gateway IP address to which the router sends all IP packets for which it does not have a learned or static route.
It is configured with a higher administrative distance than the original dynamic routing protocol has.
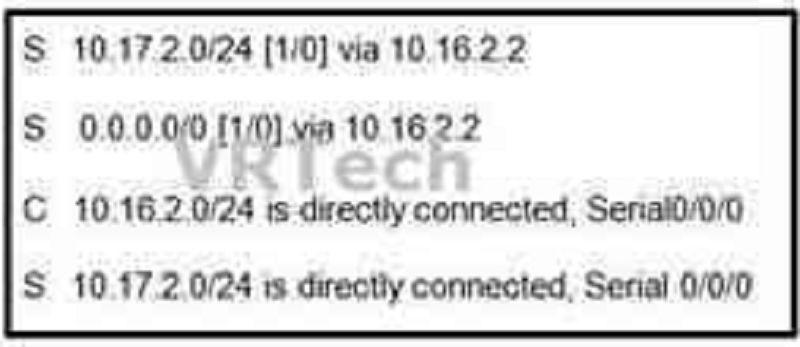
4 Refer to the exhibit. Which route was configured as a static route to a specific network using the next-hop address?
S 10.17.2.0/24 [1/0] via 10.16.2.2
S 0.0.0.0/0 [1/0] via 10.16.2.2
C 10.16.2.0/24 is directly connected, Serial0/0/0
S 10.17.2.0/24 is directly connected, Serial 0/0/0
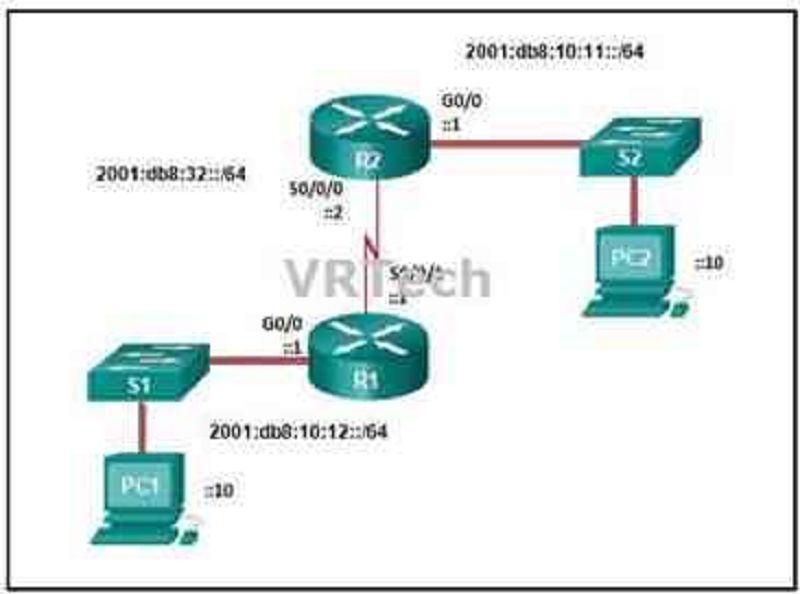
5 Refer to the exhibit. Which command will properly configure an IPv6 static route on R2 that will allow traffic from PC2 to reach PC1 without any recursive lookups by router R2?
R2(config)# ipv6 route 2001:db8:10:12::/64 2001:db8:32::1
R2(config)# ipv6 route 2001:db8:10:12::/64 S0/0/0
R2(config)# ipv6 route ::/0 2001:db8:32::1
R2(config)# ipv6 route 2001:db8:10:12::/64 S0/0/1
6 A router has used the OSPF protocol to learn a route to the 172.16.32.0/19 network. Which command will implement a backup floating static route to this network?
Ip route 172.16.0.0 255.255.240.0 S0/0/0 200
Ip route 172.16.32.0 255.255.224.0 S0/0/0 200
Ip route 172.16.0.0 255.255.224.0 S0/0/0 100
Ip route 172.16.32.0 255.255.0.0 S0/0/0 100

7 Refer to the exhibit. An administrator is attempting to install an IPv6 static route on router R1 to reach the network attached to router R2. After the static route command is entered, connectivity to the network is still failing. What error has been made in the static route configuration?
The network prefix is incorrect.
The destination network is incorrect.
The interface is incorrect.
The next hop address is incorrect.
8 Which statement describes a route that has been learned dynamically?
It is automatically updated and maintained by routing protocols.
It is unaffected by changes in the topology of the network.
It has an administrative distance of 1.
It is identified by the prefix C in the routing table.
9 Compared with dynamic routes, what are two advantages of using static routes on a router? (Choose two.)
They improve network security
They use fewer router resources.
They improve the efficiency of discovering neighboring networks.
They take less time to converge when the network topology changes.
They automatically switch the path to the destination network when the topology changes.
10 To enable RIP routing for a specific subnet, the configuration command network 172.16.64.32 was entered by the network administrator. What address, if any, appears in the running configuration file to identify this network?
172.16.64.32
172.16.64.0
172.16.0.0
No address is displayed.

11 Refer to the exhibit. What is the administrative distance value that indicates the route for R2 to reach the 10.10.0.0/16 network?
110
1
782
0
12 Which route will a router use to forward an IPv4 packet after examining its routing table for the best match with the destination address?
A level 1 child route
A level 1 parent route
A level 1 ultimate route
A level 2 supernet route
13 Which two factors are important when deciding which interior gateway routing protocol to use? (Choose two.)
Scalability
ISP selection
Speed of convergence
The autonomous system that is used
Campus backbone architecture
14 Employees of a company connect their wireless laptop computers to the enterprise LAN via wireless access points that are cabled to the Ethernet ports of switches. At which layer of the three-layer hierarchical network design model do these switches operate?
Distribution
Data link
Physical
Access
Core
15 Which network design may be recommended for a small campus site that consists of a single building with a few users?
A network design where the access and core layers are collapsed into a single layer
A collapsed core network design
A three-tier campus network design where the access, distribution, and core are all separate layers, each one with very specific functions
A network design where the access and distribution layers are collapsed into a single layer
16 Which information does a switch use to keep the MAC address table information current?
The destination MAC address and the incoming port
The destination MAC address and the outgoing port
The source and destination MAC addresses and the incoming port
The source and destination MAC addresses and the outgoing port
The source MAC address and the incoming port
The source MAC address and the outgoing port
17 Which advantage does the store-and-forward switching method have compared with the cut-through switching method?
Collision detecting
Frame error checking
Faster frame forwarding
Frame forwarding using IPv4 Layer 3 and 4 information
18 Which characteristic describes cut-through switching?
Error-free fragments are forwarded, so switching occurs with lower latency.
Frames are forwarded without any error checking.
Only outgoing frames are checked for errors.
Buffering is used to support different Ethernet speeds.
19 What is a result of connecting two or more switches together?
The number of broadcast domains is increased.
The size of the broadcast domain is increased.
The number of collision domains is reduced.
The size of the collision domain is increased.
20 In what situation would a Layer 2 switch have an IP address configured?
When the Layer 2 switch needs to forward user traffic to another device
When the Layer 2 switch is the default gateway of user traffic
When the Layer 2 switch needs to be remotely managed
When the Layer 2 switch is using a routed port
21 A network administrator is configuring a new Cisco switch for remote management access. Which three items must be configured on the switch for the task? (Choose three.)
IP address
VTP domain
Vty lines
Default VLAN
Default gateway
Loopback address
22 As part of the new security policy, all switches on the network are configured to automatically learn MAC addresses for each port. All running configurations are saved at the start and close of every business day. A severe thunderstorm causes an extended power outage several hours after the close of business. When the switches are brought back online, the dynamically learned MAC addresses are retained. Which port security configuration enabled this?
Auto secure MAC addresses
Dynamic secure MAC addresses
Static secure MAC addresses
Sticky secure MAC addresses
23 A network administrator is configuring port security on a Cisco switch. When a violation occurs, which violation mode that is configured on an interface will cause packets with an unknown source address to be dropped with no notification sent?
Off
Restrict
Protect
Shutdown
24 Which commands are used to re-enable a port that has been disabled as a result of a port security violation?
Shutdown no shutdown
Shutdown no switchport port-security
Shutdown no switchport port-security violation shutdown
Shutdown no switchport port-security maximum
25 Which two characteristics describe the native VLAN? (Choose two.)
Designed to carry traffic that is generated by users, this type of VLAN is also known as the default VLAN
The native VLAN traffic will be untagged across the trunk link.
This VLAN is necessary for remote management of a switch.
High priority traffic, such as voice traffic, uses the native VLAN.
The native VLAN provides a common identifier to both ends of a trunk.
26 Which type of traffic is designed for a native VLAN?
User-generated
Tagged
Untagged
Management
27 An administrator is trying to remove configurations from a switch. After using the command erase startup-config and reloading the switch, the administrator finds that VLANs 10 and 100 still exist on the switch. Why were these VLANs not removed?
These VLANs are default VLANs that cannot be removed.
These VLANs cannot be deleted unless the switch is in VTP client mode.
These VLANs can only be removed from the switch by using the no vlan 10 and no vlan 100 commands.
Because these VLANs are stored in a file that is called vlan.dat that is located in flash memory, this file must be manually deleted.
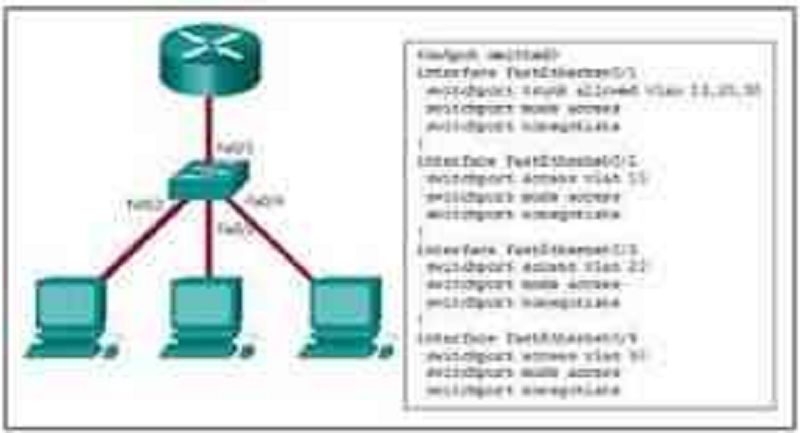
28 Refer to the exhibit. Inter-VLAN communication between VLAN 10, VLAN 20, and VLAN 30 is not successful. What is the problem?
The access interfaces do not have IP addresses and each should be configured with an IP address.
The switch interface FastEthernet0/1 is configured as an access interface and should be configured as a trunk interface.
The switch interface FastEthernet0/1 is configured to not negotiate and should be configured to negotiate.
The switch interfaces FastEthernet0/2, FastEthernet0/3, and FastEthernet0/4 are configured to not negotiate and should be configured to negotiate.
29 A network administrator is configuring an ACL with the command access-list 10 permit 172.16.32.0 0.0.15.255. Which IPv4 address matches the ACE?
172.16.20.2
172.16.26.254
172.16.36.255
172.16.48.5
30 The computers used by the network administrators for a school are on the 10.7.0.0/27 network. Which two commands are needed at a minimum to apply an ACL that will ensure that only devices that are used by the network administrators will be allowed Telnet access to the routers? (Choose two.
Access-class 5 in
Access-list 5 deny any
Access-list standard VTY permit 10.7.0.0 0.0.0.127
Access-list 5 permit 10.7.0.0 0.0.0.31
Ip access-group 5 out
Ip access-group 5 in
31 A network engineer has created a standard ACL to control SSH access to a router. Which command will apply the ACL to the VTY lines?
Access-group 11 in
Access-class 11 in
Access-list 11 in
Access-list 110 in
32 Which set of commands will configure a router as a DHCP server that will assign IPv4 addresses to the 192.168.100.0/23 LAN while reserving the first 10 and the last addresses for static assignment?
Ip dhcp excluded-address 192.168.100.1 192.168.100.10 ip dhcp excluded-address 192.168.100.254 ip dhcp pool LAN-POOL-100 network 192.168.100.0 255.255.255.0 ip default-gateway 192.168.100.1
Ip dhcp excluded-address 192.168.100.1 192.168.100.10 ip dhcp excluded-address 192.168.101.254 ip dhcp pool LAN-POOL-100 network 192.168.100.0 255.255.254.0 default-router 192.168.100.1
Dhcp pool LAN-POOL-100 ip dhcp excluded-address 192.168.100.1 192.168.100.9 ip dhcp excluded-address 192.168.100.254 network 192.168.100.0 255.255.254.0 default-router 192.168.101.1
Ip dhcp excluded-address 192.168.100.1 192.168.100.9 ip dhcp excluded-address 192.168.101.254 ip dhcp pool LAN-POOL-100 ip network 192.168.100.0 255.255.254.0 ip default-gateway 192.168.100.1

33 Refer to the exhibit. R1 has been configured as shown. However, PC1 is not able to receive an IPv4 address. What is the problem?
A DHCP server must be installed on the same LAN as the host that is receiving the IP address.
R1 is not configured as a DHCPv4 server.
The ip address dhcp command was not issued on the interface Gi0/1.
The ip helper-address command was applied on the wrong interface.
34 What is used in the EUI-64 process to create an IPv6 interface ID on an IPv6 enabled interface?
The MAC address of the IPv6 enabled interface
A randomly generated 64-bit hexadecimal address
An IPv6 address that is provided by a DHCPv6 server
An IPv4 address that is configured on the interface

35 Refer to the exhibit. Which statement shown in the output allows router R1 to respond to stateless DHCPv6 requests?
Ipv6 unicast-routing
Dns-server 2001:DB8:8::8
Ipv6 dhcp server LAN1
Ipv6 nd other-config-flag
Prefix-delegation 2001:DB8:8::/48 00030001000E84244E70

36 Refer to the exhibit. NAT is configured on Remote and Main. The PC is sending a request to the web server. What IPv4 address is the source IP address in the packet between Main and the web server?
10.130.5.76
209.165.200.245
203.0.113.5
172.16.1.10
192.0.2.1
209.165.200.226
37 Which type of traffic would most likely have problems when passing through a NAT device?
Telnet
IPsec
HTTP
ICMP
DNS
38 A small company has a web server in the office that is accessible from the Internet. The IP address 192.168.10.15 is assigned to the web server. The network administrator is configuring the router so that external clients can access the web server over the Internet. Which item is required in the NAT configuration?
An IPv4 address pool
An ACL to identify the local IPv4 address of the web server
The keyword overload for the ip nat inside source command
The ip nat inside source command to link the inside local and inside global addresses
39 Which configuration would be appropriate for a small business that has the public IP address of 209.165.200.225/30 assigned to the external interface on the router that connects to the Internet?
Access-list 1 permit 10.0.0.0 0.255.255.255 ip nat inside source list 1 interface serial 0/0/0 overload
Access-list 1 permit 10.0.0.0 0.255.255.255 ip nat pool comp 192.168.2.1 192.168.2.8 netmask 255.255.255.240 ip nat inside source list 1 pool comp
Access-list 1 permit 10.0.0.0 0.255.255.255 ip nat pool comp 192.168.2.1 192.168.2.8 netmask 255.255.255.240 ip nat inside source list 1 pool comp overload
Access-list 1 permit 10.0.0.0 0.255.255.255 ip nat pool comp 192.168.2.1 192.168.2.8 netmask 255.255.255.240 ip nat inside source list 1 pool comp overload ip nat inside source static 10.0.0.5 209.165.200.225
40 What benefit does NAT64 provide?
It allows sites to use private IPv6 addresses and translates them to global IPv6 addresses.
It allows sites to connect multiple IPv4 hosts to the Internet via the use of a single public IPv4 address.
It allows sites to connect IPv6 hosts to an IPv4 network by translating the IPv6 addresses to IPv4 addresses.
It allows sites to use private IPv4 addresses, and thus hides the internal addressing structure from hosts on public IPv4 networks

41 Refer to the exhibit. A PC at address 10.1.1.45 is unable to access the Internet. What is the most likely cause of the problem?
The NAT pool has been exhausted.
The wrong netmask was used on the NAT pool.
Access-list 1 has not been configured properly.
The inside and outside interfaces have been configured backwards.
42 A network engineer is interested in obtaining specific information relevant to the operation of both distribution and access layer Cisco devices. Which command provides common information relevant to both types of devices?
Show ip protocols
Show ip interface
Show cdp neighbors
Show port-security
Show mac-address-table
43 Which two statements are correct if a configured NTP master on a network cannot reach any clock with a lower stratum number? (Choose two.)
The NTP master will claim to be synchronized at the configured stratum number.
The NTP master will be the clock with 1 as its stratum number.
An NTP server with a higher stratum number will become the master.
Other systems will be willing to synchronize to that master using NTP.
The NTP master will lower its stratum number.
44 A network administrator is verifying a configuration that involves network monitoring. What is the purpose of the global configuration command logging trap 4?
System messages will be forwarded to the number following the logging trap argument.
System messages that exist in levels 4-7 must be forwarded to a specific logging server.
System messages that match logging levels 0-4 will be forwarded to a specified logging device.
System messages will be forwarded using a SNMP version that matches the argument that follows the logging trap command
45 Refer to the exhibit. An administrator is examining the message in a syslog server. What can be determined from the message?
This is a notification message for a normal but significant condition.
This is an alert message for which immediate action is needed.
This is an error message for which warning conditions exist.
This is an error message that indicates the system is unusable.
46 What is indicated by the M in the Cisco IOS image name c1900-universalk9-mz.SPA.153-3.M.bin?
A maintenance deployment release
A minor release
A mainline release
An extended maintenance release

47 Refer to the exhibit. A network engineer is preparing to upgrade the IOS system image on a Cisco 2901 router. Based on the output shown, how much space is available for the new image?
25574400 bytes
249856000 bytes
221896413 bytes
33591768 bytes

48 Refer to the exhibit. Based on the exhibited configuration and output, why is VLAN 99 missing?
Because there is a cabling problem on VLAN 99
Because VLAN 99 is not a valid management VLAN
Because VLAN 1 is up and there can only be one management VLAN on the switch
Because VLAN 99 needs to be entered as a VLAN under an interface before it can become an active interface
Because the VLAN 99 has not been manually entered into the VLAN database with the vlan 99 command
{"name":"B", "url":"https://www.quiz-maker.com/QPREVIEW","txt":"Test your knowledge on networking fundamentals with this comprehensive quiz designed for networking enthusiasts and professionals alike. Dive into various topics including routing protocols, VLANs, IP addressing, and more.With 49 challenging questions, you can:Assess your current networking knowledgeIdentify areas for improvementPrepare for networking certifications","img":"https:/images/course5.png"}
More Quizzes
NMO MQF
8744160
Geggegeeg
1478
NAV GENERAL PPL
2412100
Cherie's 30th!
201024
What Would You Be Famous For? Free Personality
201018247
What Is My Favorite Movie - Free Online
201018631
Which Meme Are You Today? - Free, Instant Results
201018027
Grand Tour - Can You Ace These Questions?
201018322
Are You a Federalist or Anti-Federalist? Free
201016846
Camping Trivia - Test Your Outdoor Knowledge
201023152
Where Do I Fit In? Free Personality Type
201017028
Aesop Fables - Test Your Knowledge (Free Online)
201022349