Security + exam 2
Which of the following network vulnerability scan indicators BEST validates a successful, active scan?
The scan job is scheduled to run during off-peak hours.
The scan output lists SQL injection attack vectors.
The scan data identifies the use of privileged-user credentials.
The scan results identify the hostname and IP address.
An analyst wants to implement a more secure wireless authentication for office access points. Which of the following technologies allows for encrypted authentication of wireless clients over TLS?
PEAP
EAP
WPA2
RADIUS
When systems, hardware, or software are not supported by the original vendor, it is a vulnerability known as:
System sprawl
End-of-life systems
Resource exhaustion
A default configuration
A company has three divisions, each with its own networks and services. The company decides to make its secure web portal accessible to all employees utilizing their existing usernames and passwords. The security administrator has elected to use SAML to support authentication. In this scenario, which of the following will occur when users try to authenticate to the portal? (Select two.)
The portal will function as a service provider and request an authentication assertion.
The portal will function as an identity provider and issue an authentication assertion.
The portal will request an authentication ticket from each network that is transitively trusted.
The back-end networks will function as an identity provider and issue an authentication assertion.
The back-end networks will request authentication tickets from the portal, which will act as the third-party service provider authentication store.
The back-end networks will verify the assertion token issued by the portal functioning as the identity provider.
A company wants to host a publicity available server that performs the following functions: Evaluates MX record lookup Can perform authenticated requests for A and AAA records Uses RRSIG Which of the following should the company use to fulfill the above requirements?
LDAPS
DNSSEC
SFTP
Nslookup
Dig
A system administrator wants to provide balance between the security of a wireless network and usability. The administrator is concerned with wireless encryption compatibility of older devices used by some employees. Which of the following would provide strong security and backward compatibility when accessing the wireless network?
Open wireless network and SSL VPN
WPA using a preshared key
WPA2 using a RADIUS back-end for 802.1x authentication
WEP with a 40-bit key
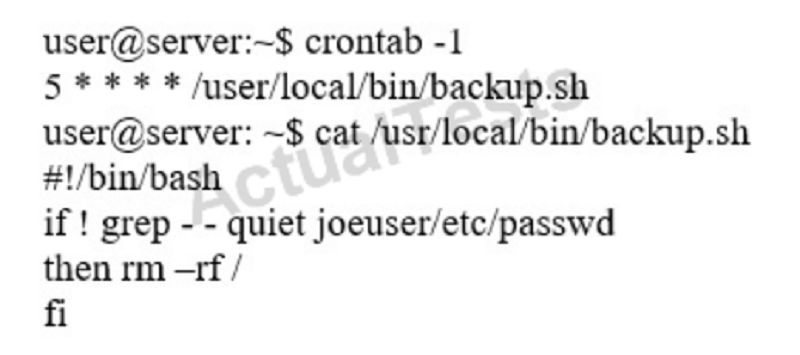
An information security specialist is reviewing the following output from a Linux server. Based on the above information, which of the following types of malware was installed on the server?
Logic bomb
Trojan
Backdoor
Ransomware
Rootkit
In terms of encrypting data, which of the following is BEST described as a way to safeguard password data by adding random data to it in storage?
Using salt
Using hash algorithms
Implementing elliptical curve
Implementing PKI
A system administrator wants to provide for and enforce wireless access accountability during events where external speakers are invited to make presentations to a mixed audience of employees and non-employees. Which of the following should the administrator implement?
Shared accounts
Preshared passwords
Least privilege
Sponsored guest
Which of the following would MOST likely appear in an uncredentialed vulnerability scan?
Self-signed certificates
Missing patches
Auditing parameters
Inactive local accounts
When identifying a company’s most valuable assets as part of a BIA, which of the following should be the FIRST priority?
Life
Intellectual property
Sensitive data
Public reputation
When considering a third-party cloud service provider, which of the following criteria would be the BEST to include in the security assessment process? (Select two.)
Use of performance analytics
Adherence to regulatory compliance
Data retention policies
Size of the corporation
Breadth of applications support
An organization needs to implement a large PKI. Network engineers are concerned that repeated transmission of the OCSP will impact network performance. Which of the following should the security analyst recommend is lieu of an OCSP?
CSR
CRL
CA
OID
Which of the following occurs when the security of a web application relies on JavaScript for input validation?
The integrity of the data is at risk.
The security of the application relies on antivirus.
A host-based firewall is required.
The application is vulnerable to race conditions.
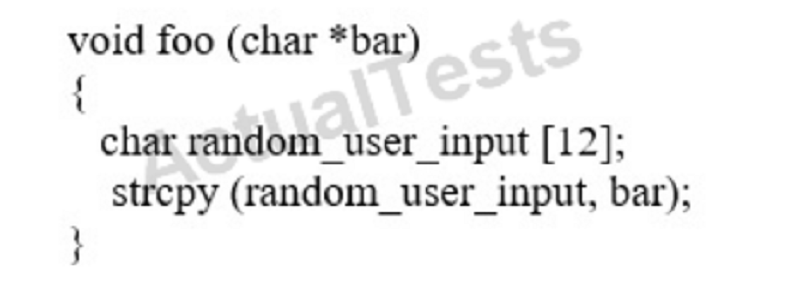
An analyst is reviewing a simple program for potential security vulnerabilities before being deployed to a Windows server. Given the following code: Which of the following vulnerabilities is present?
Bad memory pointer
Buffer overflow
Integer overflow
Backdoor
An organization's file server has been virtualized to reduce costs. Which of the following types of backups would be MOST appropriate for the particular file server?
Snapshot
Full
Incremental
Differential
A wireless network uses a RADIUS server that is connected to an authenticator, which in turn connects to a supplicant. Which of the following represents the authentication architecture in use?
Open systems authentication
Captive portal
RADIUS federation
802.1x
An employer requires that employees use a key-generating app on their smartphones to log into corporate applications. In terms of authentication of an individual, this type of access policy is BEST defined as:
Something you have.
Something you know.
Something you do.
Something you are.
Adhering to a layered security approach, a controlled access facility employs security guards who verify the authorization of all personnel entering the facility. Which of the following terms BEST describes the security control being employed?
Administrative
Corrective
Deterrent
Compensating
A security analyst is hardening a web server, which should allow a secure certificate-based session using the organization’s PKI infrastructure. The web server should also utilize the latest security techniques and standards. Given this set of requirements, which of the following techniques should the analyst implement to BEST meet these requirements? (Select two.)
Install an X- 509-compliant certificate.
Implement a CRL using an authorized CA.
Enable and configure TLS on the server.
Install a certificate signed by a public CA.
Configure the web server to use a host header.
A manager wants to distribute a report to several other managers within the company. Some of them reside in remote locations that are not connected to the domain but have a local server. Because there is sensitive data within the report and the size of the report is beyond the limit of the email attachment size, emailing the report is not an option. Which of the following protocols should be implemented to distribute the report securely? (Select three.)
S/MIME
SSH
SNMPv3
FTPS
SRTP
HTTPS
LDAPS
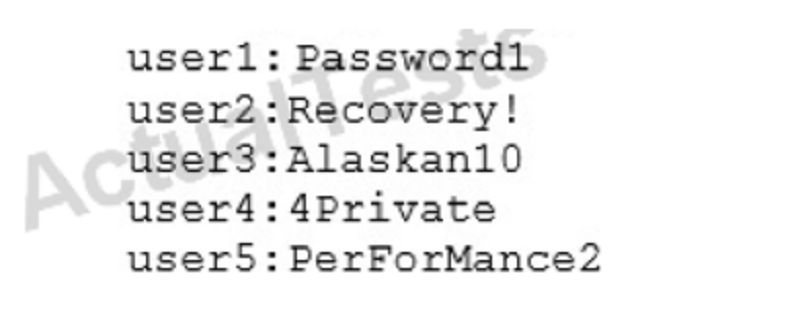
An auditor is reviewing the following output from a password-cracking tool: Which of the following methods did the author MOST likely use?
Hybrid
Dictionary
Brute force
Rainbow table
Which of the following must be intact for evidence to be admissible in court?
Chain of custody
Order of volatility
Legal hold
Preservation
A vulnerability scanner that uses its running service’s access level to better assess vulnerabilities across multiple assets within an organization is performing a:
Credentialed scan.
Non-intrusive scan.
Privilege escalation test.
Passive scan.
Which of the following cryptography algorithms will produce a fixed-length, irreversible output?
AES
3DES
RSA
MD5
A technician suspects that a system has been compromised. The technician reviews the following log entry: WARNING- hash mismatch: C:\Window\SysWOW64\user32.dl WARNING- hash mismatch: C:\Window\SysWOW64\kernel32.dll Based solely ono the above information, which of the following types of malware is MOST likely installed on the system?
Rootkit
Ransomware
Trojan
Backdoor
A new firewall has been places into service at an organization. However, a configuration has not been entered on the firewall. Employees on the network segment covered by the new firewall report they are unable to access the network. Which of the following steps should be completed to BEST resolve the issue?
The firewall should be configured to prevent user traffic form matching the implicit deny rule.
The firewall should be configured with access lists to allow inbound and outbound traffic.
The firewall should be configured with port security to allow traffic.
The firewall should be configured to include an explicit deny rule.
Which of the following are the MAIN reasons why a systems administrator would install security patches in a staging environment before the patches are applied to the production server? (Select two.)
To prevent server availability issues
To verify the appropriate patch is being installed
To generate a new baseline hash after patching
To allow users to test functionality
To ensure users are trained on new functionality
A Chief Information Officer (CIO) drafts an agreement between the organization and its employees. The agreement outlines ramifications for releasing information without consent and/or approvals. Which of the following BEST describes this type of agreement?
ISA
NDA
MOU
SLA
Which of the following would meet the requirements for multifactor authentication?
Username, PIN, and employee ID number
Fingerprint and password
Smart card and hardware token
Voice recognition and retina scan
A manager suspects that an IT employee with elevated database access may be knowingly modifying financial transactions for the benefit of a competitor. Which of the following practices should the manager implement to validate the concern?
Separation of duties
Mandatory vacations
Background checks
Security awareness training
A penetration tester finds that a company’s login credentials for the email client were being sent in clear text. Which of the following should be done to provide encrypted logins to the email server?
Enable IPSec and configure SMTP.
Enable SSH and LDAP credentials.
Enable MIME services and POP3.
Enable an SSL certificate for IMAP services.
Before an infection was detected, several of the infected devices attempted to access a URL that was similar to the company name but with two letters transported. Which of the following BEST describes the attack vector used to infect the devices?
Cross-site scripting
DNS poisoning
Typo squatting
URL hijacking
Joe, a security administrator, needs to extend the organization’s remote access functionality to be used by staff while travelling. Joe needs to maintain separate access control functionalities for internal, external, and VOIP services. Which of the following represents the BEST access technology for Joe to use?
RADIUS
TACACS+
Diameter
Kerberos
The availability of a system has been labeled as the highest priority. Which of the following should be focused on the MOST to ensure the objective?
Authentication
HVAC
Full-disk encryption
File integrity checking
As part of the SDLC, a third party is hired to perform a penetration test. The third party will have access to the source code, integration tests, and network diagrams. Which of the following BEST describes the assessment being performed?
Black box
Regression
White box
Fuzzing
A dumpster diver recovers several hard drives from a company and is able to obtain confidential data from one of the hard drives. The company then discovers its information is posted online. Which of the following methods would have MOST likely prevented the data from being exposed?
Removing the hard drive from its enclosure
Using software to repeatedly rewrite over the disk space
Using Blowfish encryption on the hard drives
Using magnetic fields to erase the data
Which of the following are methods to implement HA in a web application server environment? (Select two.)
Load balancers
Application layer firewalls
Reverse proxies
VPN concentrators
Routers
An application developer is designing an application involving secure transports from one service to another that will pass over port 80 for a request. Which of the following secure protocols is the developer MOST likely to use?
FTPS
SFTP
SSL
LDAPS
SSH
Which of the following precautions MINIMIZES the risk from network attacks directed at multifunction printers, as well as the impact on functionality at the same time?
Isolating the systems using VLANs
Installing a software-based IPS on all devices
Enabling full disk encryption
Implementing a unique user PIN access functions
After an identified security breach, an analyst is tasked to initiate the IR process. Which of the following is the NEXT step the analyst should take?
Recovery
Identification
Preparation
Documentation
Escalation
A company was recently audited by a third party. The audit revealed the company’s network devices were transferring files in the clear. Which of the following protocols should the company use to transfer files?
HTTPS
LDAPS
SCP
SNMPv3
During a monthly vulnerability scan, a server was flagged for being vulnerable to an Apache Struts exploit. Upon further investigation, the developer responsible for the server informs the security team that Apache Struts is not installed on the server. Which of the following BEST describes how the security team should reach to this incident?
The finding is a false positive and can be disregarded
The Struts module needs to be hardened on the server
The Apache software on the server needs to be patched and updated
The server has been compromised by malware and needs to be quarantined.
A systems administrator wants to protect data stored on mobile devices that are used to scan and record assets in a warehouse. The control must automatically destroy the secure container of mobile devices if they leave the warehouse. Which of the following should the administrator implement? (Select two.)
Geofencing
Remote wipe
Near-field communication
Push notification services
Containerization
A security analyst is performing a quantitative risk analysis. The risk analysis should show the potential monetary loss each time a threat or event occurs. Given this requirement, which of the following concepts would assist the analyst in determining this value? (Select two.)
ALE
AV
ARO
EF
ROI
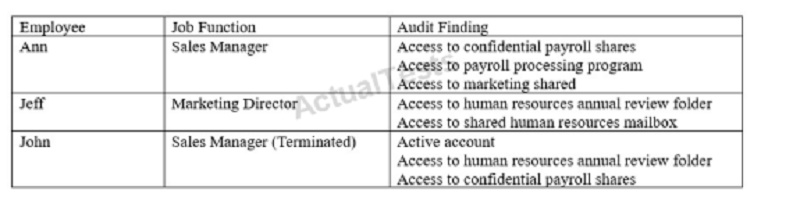
An audit takes place after company-wide restricting, in which several employees changed roles. The following deficiencies are found during the audit regarding access to confidential data: Which of the following would be the BEST method to prevent similar audit findings in the future?
Implement separation of duties for the payroll department.
Implement a DLP solution on the payroll and human resources servers.
Implement rule-based access controls on the human resources server.
Implement regular permission auditing and reviews.
A security engineer is configuring a wireless network that must support mutual authentication of the wireless client and the authentication server before users provide credentials. The wireless network must also support authentication with usernames and passwords. Which of the following authentication protocols MUST the security engineer select?
EAP-FAST
EAP-TLS
PEAP
EAP
Which of the following vulnerability types would the type of hacker known as a script kiddie be MOST dangerous against?
Passwords written on the bottom of a keyboard
Unpatched exploitable Internet-facing services
Unencrypted backup tapes
Misplaced hardware token
An in-house penetration tester is using a packet capture device to listen in on network communications. This is an example of:
Passive reconnaissance
Persistence
Escalation of privileges
Exploiting the switch
A black hat hacker is enumerating a network and wants to remain convert during the process. The hacker initiates a vulnerability scan. Given the task at hand the requirement of being convert, which of the following statements BEST indicates that the vulnerability scan meets these requirements?
The vulnerability scanner is performing an authenticated scan.
The vulnerability scanner is performing local file integrity checks.
The vulnerability scanner is performing in network sniffer mode.
The vulnerability scanner is performing banner grabbing.
A development team has adopted a new approach to projects in which feedback is iterative and multiple iterations of deployments are provided within an application’s full life cycle. Which of the following software development methodologies is the development team using?
Waterfall
Agile
Rapid
Extreme
A Chief Executive Officer (CEO) suspects someone in the lab testing environment is stealing confidential information after working hours when no one else is around. Which of the following actions can help to prevent this specific threat?
Implement time-of-day restrictions.
Audit file access times.
Secretly install a hidden surveillance camera.
Require swipe-card access to enter the lab.
A company hires a third-party firm to conduct an assessment of vulnerabilities exposed to the Internet. The firm informs the company that an exploit exists for an FTP server that had a version installed from eight years ago. The company has decided to keep the system online anyway, as no upgrade exists form the vendor. Which of the following BEST describes the reason why the vulnerability exists?
Default configuration
End-of-life system
Weak cipher suite
Zero-day threats
An organization uses SSO authentication for employee access to network resources. When an employee resigns, as per the organization’s security policy, the employee’s access to all network resources is terminated immediately. Two weeks later, the former employee sends an email to the help desk for a password reset to access payroll information from the human resources server. Which of the following represents the BEST course of action?
Approve the former employee’s request, as a password reset would give the former employee access to only the human resources server.
Deny the former employee’s request, since the password reset request came from an external email address.
Deny the former employee’s request, as a password reset would give the employee access to all network resources.
Approve the former employee’s request, as there would not be a security issue with the former employee gaining access to network resources.
Joe, a user, wants to send Ann, another user, a confidential document electronically. Which of the following should Joe do to ensure the document is protected from eavesdropping?
Encrypt it with Joe’s private key
Encrypt it with Joe’s public key
Encrypt it with Ann’s private key
Encrypt it with Ann’s public key
A director of IR is reviewing a report regarding several recent breaches. The director compiles the following statistic’s -Initial IR engagement time frame -Length of time before an executive management notice went out -Average IR phase completion The director wants to use the data to shorten the response time. Which of the following would accomplish this?
CSIRT
Containment phase
Escalation notifications
Tabletop exercise
To reduce disk consumption, an organization’s legal department has recently approved a new policy setting the data retention period for sent email at six months. Which of the following is the BEST way to ensure this goal is met?
Create a daily encrypted backup of the relevant emails.
Configure the email server to delete the relevant emails.
Migrate the relevant emails into an “Archived” folder.
Implement automatic disk compression on email servers.
A security administrator is configuring a new network segment, which contains devices that will be accessed by external users, such as web and FTP server. Which of the following represents the MOST secure way to configure the new network segment?
The segment should be placed on a separate VLAN, and the firewall rules should be configured to allow external traffic.
The segment should be placed in the existing internal VLAN to allow internal traffic only.
The segment should be placed on an intranet, and the firewall rules should be configured to allow external traffic.
The segment should be placed on an extranet, and the firewall rules should be configured to allow both internal and external traffic.
Which of the following types of attacks precedes the installation of a rootkit on a server?
Pharming
DDoS
Privilege escalation
DoS
Which of the following cryptographic algorithms is irreversible?
RC4
SHA-256
DES
AES
A security analyst receives an alert from a WAF with the following payload: var data= “” ++ <../../../../../../etc/passwd>” Which of the following types of attacks is this?
Cross-site request forgery
Buffer overflow
SQL injection
JavaScript data insertion
Firewall evasion script
A workstation puts out a network request to locate another system. Joe, a hacker on the network, responds before the real system does, and he tricks the workstation into communicating with him. Which of the following BEST describes what occurred?
The hacker used a race condition.
The hacker used a pass-the-hash attack.
The hacker-exploited importer key management.
The hacker exploited weak switch configuration.
A security analyst wants to harden the company’s VoIP PBX. The analyst is worried that credentials may be intercepted and compromised when IP phones authenticate with the BPX. Which of the following would best prevent this from occurring?
Implement SRTP between the phones and the PBX.
Place the phones and PBX in their own VLAN.
Restrict the phone connections to the PBX.
Require SIPS on connections to the PBX.
An organization is comparing and contrasting migration from its standard desktop configuration to the newest version of the platform. Before this can happen, the Chief Information Security Officer (CISO) voices the need to evaluate the functionality of the newer desktop platform to ensure interoperability with existing software in use by the organization. In which of the following principles of architecture and design is the CISO engaging?
Dynamic analysis
Change management
Baselining
Waterfalling
A security administrator suspects a MITM attack aimed at impersonating the default gateway is underway. Which of the following tools should the administrator use to detect this attack? (Select two)
Ping
Ipconfig
Tracert
Netstat
Dig
Nslookup
A user is presented with the following items during the new-hire onboarding process: -Laptop -Secure USB drive -Hardware OTP token -External high-capacity HDD -Password complexity policy -Acceptable use policy -HASP key -Cable lock Which of the following is one component of multifactor authentication?
Secure USB drive
Cable lock
Hardware OTP token
HASP key
An organization requires users to provide their fingerprints to access an application. To improve security, the application developers intend to implement multifactor authentication. Which of the following should be implemented?
Use a camera for facial recognition
Have users sign their name naturally
Require a palm geometry scan
Implement iris recognition
A network technician is setting up a segmented network that will utilize a separate ISP to provide wireless access to the public area for a company. Which of the following wireless security methods should the technician implement to provide basic accountability for access to the public network?
Pre-shared key
Enterprise
Wi-Fi Protected setup
Captive portal
After a routine audit, a company discovers that engineering documents have been leaving the network on a particular port. The company must allow outbound traffic on this port, as it has a legitimate business use. Blocking the port would cause an outage. Which of the following technology controls should the company implement?
NAC
Web proxy
DLP u
ACL
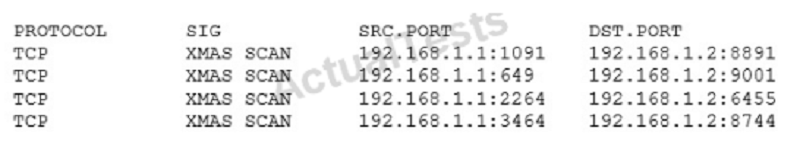
A security analyst has received the following alert snippet from the HIDS appliance: Given the above logs, which of the following is the cause of the attack?
The TCP ports on destination are all open
FIN, URG, and PSH flags are set in the packet header
TCP MSS is configured improperly
There is improper Layer 2 segmentation
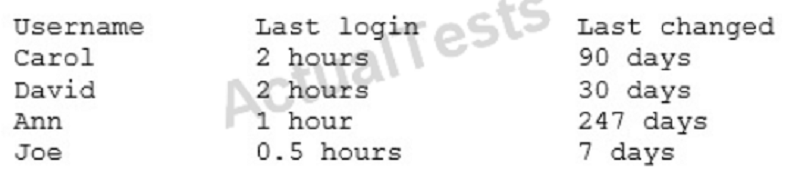
A company’s AUP requires: Passwords must meet complexity requirements. Passwords are changed at least once every six months. Passwords must be at least eight characters long. An auditor is reviewing the following report: Which of the following controls should the auditor recommend to enforce the AUP?
Account lockout thresholds
Account recovery
Password expiration
Prohibit password reuse
An organization’s primary datacenter is experiencing a two-day outage due to an HVAC malfunction. The node located in the datacenter has lost power and is no longer operational, impacting the ability of all users to connect to the alternate datacenter. Which of the following BIA concepts BEST represents the risk described in this scenario?
SPoF
RTO
MTBF
MTTR
A security analyst notices anomalous activity coming from several workstations in the organizations. Upon identifying and containing the issue, which of the following should the security analyst do NEXT?
Document and lock the workstations in a secure area to establish chain of custody
Notify the IT department that the workstations are to be reimaged and the data restored for reuse
Notify the IT department that the workstations may be reconnected to the network for the users to continue working
Document findings and processes in the after-action and lessons learned report
An employee receives an email, which appears to be from the Chief Executive Officer (CEO), asking for a report of security credentials for all users. Which of the following types of attack is MOST likely occurring?
Policy violation
Social engineering
Whaling
Spear phishing
An information security analyst needs to work with an employee who can answer questions about how data for a specific system is used in the business. The analyst should seek out an employee who has the role of:
Steward
Owner
Privacy officer
Systems administrator
A group of non-profit agencies wants to implement a cloud service to share resources with each other and minimize costs. Which of the following cloud deployment models BEST describes this type of effort?
Public
Hybrid
Community
Private
A copy of a highly confidential salary report was recently found on a printer in the IT department. The human resources department does not have this specific printer mapped to its devices, and it is suspected that an employee in the IT department browsed to the share where the report was located and printed it without authorization. Which of the following technical controls would be the BEST choice to immediately prevent this from happening again?
Implement a DLP solution and classify the report as confidential, restricting access only to human resources staff
Restrict access to the share where the report resides to only human resources employees and enable auditing
Have all members of the IT department review and sign the AUP and disciplinary policies
Place the human resources computers on a restricted VLAN and configure the ACL to prevent access from the IT department
A company is developing a new system that will unlock a computer automatically when an authorized user sits in front of it, and then lock the computer when the user leaves. The user does not have to perform any action for this process to occur. Which of the following technologies provides this capability?
Facial recognition
Fingerprint scanner
Motion detector
Smart cards
A security analyst accesses corporate web pages and inputs random data in the forms. The response received includes the type of database used and SQL commands that the database accepts. Which of the following should the security analyst use to prevent this vulnerability?
Application fuzzing
Error handling
Input validation
Pointer dereference
Which of the following differentiates a collision attack from a rainbow table attack?
A rainbow table attack performs a hash lookup
A rainbow table attack uses the hash as a password
In a collision attack, the hash and the input data are equivalent
In a collision attack, the same input results in different hashes
A help desk is troubleshooting user reports that the corporate website is presenting untrusted certificate errors to employees and customers when they visit the website. Which of the following is the MOST likely cause of this error, provided the certificate has not expired?
The certificate was self signed, and the CA was not imported by employees or customers
The root CA has revoked the certificate of the intermediate CA
The valid period for the certificate has passed, and a new certificate has not been issued
The key escrow server has blocked the certificate from being validated
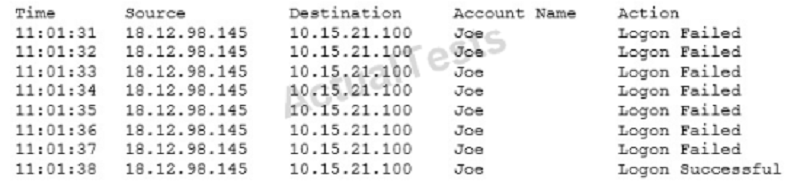
A security analyst is investigating a suspected security breach and discovers the following in the logs of the potentially compromised server: Which of the following would be the BEST method for preventing this type of suspected attack in the future?
Implement password expirations
Implement restrictions on shared credentials
Implement account lockout settings
Implement time-of-day restrictions on this server
A security administrator is trying to encrypt communication. For which of the following reasons should administrator take advantage of the Subject Alternative Name (SAM) attribute of a certificate?
It can protect multiple domains
It provides extended site validation
It does not require a trusted certificate authority
It protects unlimited subdomains
After a merger between two companies a security analyst has been asked to ensure that the organization's systems are secured against infiltration by any former employees that were terminated during the transition. Which of the following actions are MOST appropriate to harden applications against infiltration by former employees? (Select TWO)
Monitor VPN client access
Reduce failed login out settings
Develop and implement updated access control policies
Review and address invalid login attempts
Increase password complexity requirements
Assess and eliminate inactive accounts
A new mobile application is being developed in-house. Security reviews did not pick up any major flaws, however vulnerability scanning results show fundamental issues at the very end of the project cycle. Which of the following security activities should also have been performed to discover vulnerabilities earlier in the lifecycle?
Architecture review
Risk assessment
Protocol analysis
Code review
A security administrator is creating a subnet on one of the corporate firewall interfaces to use as a DMZ which is expected to accommodate at most 14 physical hosts. Which of the following subnets would BEST meet the requirements?
192.168.0.16 255.25.255.248
192.168.0.16/28
192.168.1.50 255.255.25.240
192.168.2.32/27
A company has a security policy that specifies all endpoint computing devices should be assigned a unique identifier that can be tracked via an inventory management system. Recent changes to airline security regulations have cause many executives in the company to travel with mini tablet devices instead of laptops. These tablet devices are difficult to tag and track. An RDP application is used from the tablet to connect into the company network. Which of the following should be implemented in order to meet the security policy requirements?
Virtual desktop infrastructure (IDI)
WS-security and geo-fencing
A hardware security module (HSM)
RFID tagging system
MDM software
Security Requirements Traceability Matrix (SRTM)
The security administrator receives an email on a non-company account from a coworker stating that some reports are not exporting correctly. Attached to the email was an example report file with several customers' names and credit card numbers with the PIN. Which of the following is the BEST technical controls that will help mitigate this risk of disclosing sensitive data?
Configure the mail server to require TLS connections for every email to ensure all transport data is encrypted
Create a user training program to identify the correct use of email and perform regular audits to ensure compliance
Implement a DLP solution on the email gateway to scan email and remove sensitive data or files
Classify all data according to its sensitivity and inform the users of data that is prohibited to share
{"name":"Security + exam 2", "url":"https://www.quiz-maker.com/QPREVIEW","txt":"Which of the following network vulnerability scan indicators BEST validates a successful, active scan?, An analyst wants to implement a more secure wireless authentication for office access points. Which of the following technologies allows for encrypted authentication of wireless clients over TLS?, When systems, hardware, or software are not supported by the original vendor, it is a vulnerability known as:","img":"https://www.quiz-maker.com/3012/CDN/87-4211928/security-.png?sz=1200"}
More Quizzes
Interpreter Training 2: Third Party Dial-outs
520
Geography Test: North America
14712
NorState Trivia
9432
Class Quiz
7416
Shadow Self - What Is My Shadow?
201017358
Howard Stern - Test Your Superfan Knowledge
201021762
Biology CLEP Practice Test - Free Online
201016624
Galaxies & the Universe Practice - Free Online
15815300
Are Dog Breeds Capitalized? Spelling and Case
201019141
Pronunciation Test Online - Free with Instant Results
201016624
Arrested Development Trivia - Michael Cera Edition
201018339
Am I Annoying - Are You Irritating to Others?
201018415