Testing Quiz Part 2
What subnet mask is needed if an IPv4 network has 40 devices that need IP addresses and address space is not to be wasted?
255.255.255.0
255.255.255.128
255.255.255.192
255.255.255.224
255.255.255.240
What are two characteristics shared by TCP and UDP? (Choose two.)
Default window size
Connectionless communication
Port numbering
3-way handshake
Ability to to carry digitized voice
Use of checksum
Why are port numbers included in the TCP header of a segment?
To indicate the correct router interface that should be used to forward a segment
To identify which switch ports should receive or forward the segment
To determine which Layer 3 protocol should be used to encapsulate the data
To enable a receiving host to forward the data to the appropriate application
To allow the receiving host to assemble the packet in the proper order
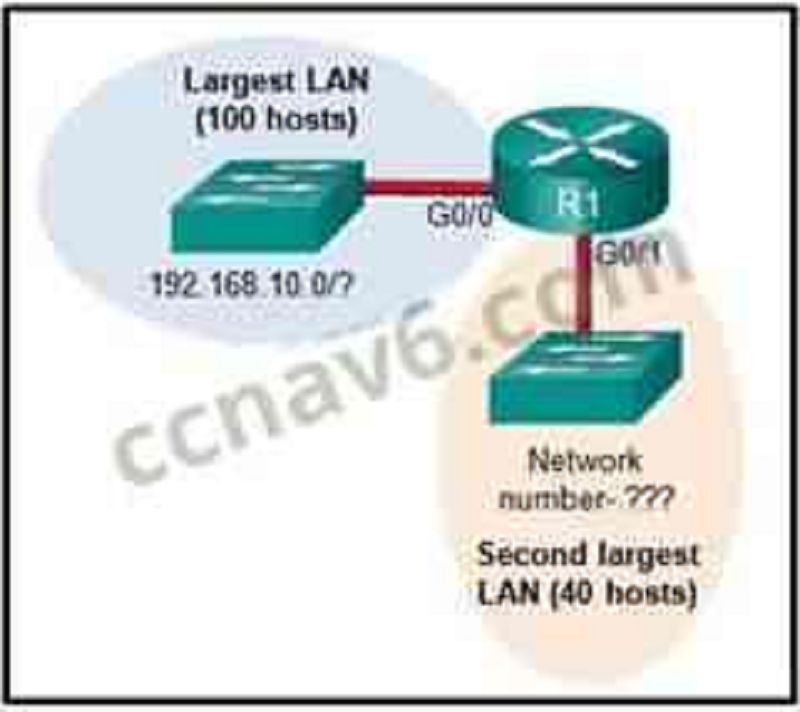
Refer to the exhibit. Consider the IP address of 192.168.10.0/24 that has been assigned to a high school building. The largest network in this building has 100 devices. If 192.168.10.0 is the network number for the largest network, what would be the network number for the next largest network, which has 40 devices?
192.168.10.0
192.168.10.128
192.168.10.192
192.168.10.224
192.168.10.240
Which statement is true about variable-length subnet masking?
Each subnet is the same size.
The size of each subnet may be different, depending on requirements.
Subnets may only be subnetted one additional time.
Bits are returned, rather than borrowed, to create additional subnets.
In what two situations would UDP be the preferred transport protocol over TCP? (Choose two.)
When applications need to guarantee that a packet arrives intact, in sequence, and unduplicated
When a faster delivery mechanism is needed
When delivery overhead is not an issue
When applications do not need to guarantee delivery of the data
When destination port numbers are dynamic
What important information is added to the TCP/IP transport layer header to ensure communication and connectivity with a remote network device?
Timing and synchronization
Destination and source port numbers
Destination and source physical addresses
Destination and source logical network addresses
What is the TCP mechanism used in congestion avoidance?
Three-way handshake
Socket pair
Two-way handshake
Sliding window
Which scenario describes a function provided by the transport layer?
A student is using a classroom VoIP phone to call home. The unique identifier burned into the phone is a transport layer address used to contact another network device on the same network.
A student is playing a short web-based movie with sound. The movie and sound are encoded within the transport layer header.
A student has two web browser windows open in order to access two web sites. The transport layer ensures the correct web page is delivered to the correct browser window.
A corporate worker is accessing a web server located on a corporate network. The transport layer formats the screen so the web page appears properly no matter what device is being used to view the web site.
A user opens three browsers on the same PC to access www.cisco.com to search for certification course information. The Cisco web server sends a datagram as a reply to the request from one of the web browsers. Which information is used by the TCP/IP protocol stack in the PC to identify which of the three web browsers should receive the reply?
The destination IP address
The destination port number
The source IP address
The source port number
What are two ways that TCP uses the sequence numbers in a segment? (Choose two.)
To identify missing segments at the destination
To reassemble the segments at the remote location
To specify the order in which the segments travel from source to destination
To limit the number of segments that can be sent out of an interface at one time
To determine if the packet changed during transit
Which two tasks are functions of the presentation layer? (Choose two.)
Compression
Addressing
Encryption
Session control
Authentication
Which three statements characterize UDP? (Choose three.)
UDP provides basic connectionless transport layer functions.
UDP provides connection-oriented, fast transport of data at Layer 3.
UDP relies on application layer protocols for error detection.
UDP is a low overhead protocol that does not provide sequencing or flow control mechanisms.
UDP relies on IP for error detection and recovery.
UDP provides sophisticated flow control mechanisms.
What is a key characteristic of the peer-to-peer networking model?
Wireless networking
Social networking without the Internet
Network printing using a print server
Resource sharing without a dedicated server*
A technician can ping the IP address of the web server of a remote company but cannot successfully ping the URL address of the same web server. Which software utility can the technician use to diagnose the problem?
Tracert
Ipconfig
Netstat
Nslookup
Which domain name would be an example of a top-level domain?
Www.cisco.com
Cisco.com
.com
Root.cisco.com
A PC obtains its IP address from a DHCP server. If the PC is taken off the network for repair, what happens to the IP address configuration?
The configuration is permanent and nothing changes.
The address lease is automatically renewed until the PC is returned.
The address is returned to the pool for reuse when the lease expires.*
The configuration is held by the server to be reissued when the PC is returned.
When planning for network growth, where in the network should packet captures take place to assess network traffic?
On as many different network segments as possible
Only at the edge of the network
Between hosts and the default gateway
Only on the busiest network segment
A wireless host needs to request an IP address. What protocol would be used to process the request?
FTP
HTTP
DHCP
ICMP
SNMP
Which example of malicious code would be classified as a Trojan horse?
Malware that was written to look like a video game
Malware that requires manual user intervention to spread between systems
Malware that attaches itself to a legitimate program and spreads to other programs when launched
Malware that can automatically spread from one system to another by exploiting a vulnerability in the target
When applied to a router, which command would help mitigate brute-force password attacks against the router?
Exec-timeout 30
Service password-encryption
Banner motd $Max failed logins = 5$
Login block-for 60 attempts 5 within 60
A network technician suspects that a particular network connection between two Cisco switches is having a duplex mismatch. Which command would the technician use to see the Layer 1 and Layer 2 details of a switch port?
Show mac-address-table
Show ip interface brief
Show interfaces
Show running-config
Where are Cisco IOS debug output messages sent by default?
Syslog server
Console line
Memory buffers
Vty lines

Refer to the exhibit. An administrator is testing connectivity to a remote device with the IP address 10.1.1.1. What does the output of this command indicate?
Connectivity to the remote device was successful.
A router along the path did not have a route to the destination.
A ping packet is being blocked by a security device along the path.
The connection timed out while waiting for a reply from the remote device.
A user is unable to reach the web site when typing http://www.cisco.com in a web browser, but can reach the same site by typing http://72.163.4.161. What is the issue?
Default gateway
DHCP
TCP/IP protocol stack
DNS
A company is expanding its business to other countries. All branch offices must remain connected to corporate headquarters at all times. Which network technology is required to support this requirement?
LAN
MAN
WAN
WLAN
A home user is looking for an ISP connection that provides high speed digital transmission over regular phone lines. What ISP connection type should be used?
DSL
Dial-up
Satellite
Cell modem
Cable modem
How does quality of service help a network support a wide range of applications and services?
By limiting the impact of a network failure
By allowing quick recovery from network failures
By providing mechanisms to manage congested network traffic
By providing the ability for the network to grow to accommodate new users
What source IP address does a router use by default when the traceroute command is issued?
The highest configured IP address on the router
The lowest configured IP address on the router
A loopback IP address
The IP address of the outbound interface
After making configuration changes on a Cisco switch, a network administrator issues a copy running-config startup-config command. What is the result of issuing this command?
The new configuration will be stored in flash memory.
The new configuration will be loaded if the switch is restarted.
The current IOS file will be replaced with the newly configured file.
The configuration changes will be removed and the original configuration will be restored.
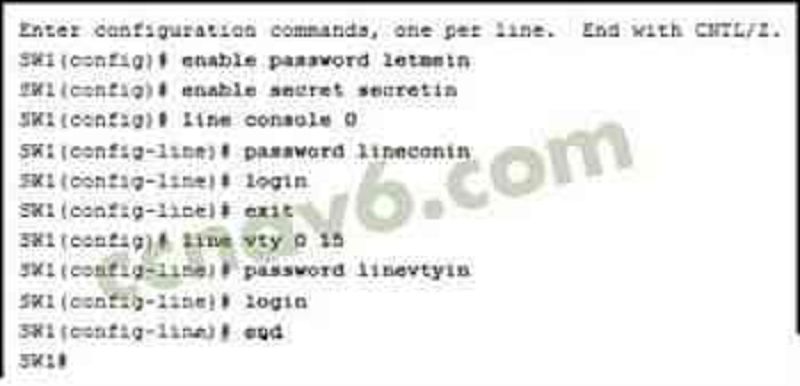
Refer to the exhibit. A network administrator is configuring access control to switch SW1. If the administrator has already logged into a Telnet session on the switch, which password is needed to access privileged EXEC mode?
Letmein
Secretin
lineconin
Linevtyin
Which connection provides a secure CLI session with encryption to a Cisco network device?
A console connection
An AUX connection
A Telnet connection
An SSH connection
What function does pressing the Tab key have when entering a command in IOS?
It aborts the current command and returns to configuration mode.
It exits configuration mode and returns to user EXEC mode.
It moves the cursor to the beginning of the next line.
It completes the remainder of a partially typed word in a command.
What layer is responsible for routing messages through an internetwork in the TCP/IP model?
Internet
Transport
Network access
Session
Which statement accurately describes a TCP/IP encapsulation process when a PC is sending data to the network?
Data is sent from the internet layer to the network access layer.
Packets are sent from the network access layer to the transport layer.
Segments are sent from the transport layer to the internet layer.
Frames are sent from the network access layer to the internet layer.
What unique address is embedded in an Ethernet NIC and used for communication on an Ethernet network?
Host address
IP address
MAC address
Network address
K layer
Which procedure is used to reduce the effect of crosstalk in copper cables?
Requiring proper grounding connections
Twisting opposing circuit wire pairs together
Wrapping the bundle of wires with metallic shielding
Designing a cable infrastructure to avoid crosstalk interference
Avoiding sharp bends during installation
During the encapsulation process, what occurs at the data link layer for a PC connected to an Ethernet network?
An IP address is added.
The logical address is added.
The physical address is added.
The process port number is added.
What are two characteristics of Ethernet MAC addresses? (Choose two.)
They are globally unique.
They are routable on the Internet.
They are expressed as 12 hexadecimal digits.
MAC addresses use a flexible hierarchical structure.
MAC addresses must be unique for both Ethernet and serial interfaces on a device.
If a device receives an Ethernet frame of 60 bytes, what will it do?
Drop the frame
Process the frame as it is
Send an error message to the sending device
Add random data bytes to make it 64 bytes long and then forward it
Under which two circumstances will a switch flood a frame out of every port except the port that the frame was received on? (Choose two.)
The frame has the broadcast address as the destination address.
The destination address is unknown to the switch.
The source address in the frame header is the broadcast address.
The source address in the frame is a multicast address.
The destination address in the frame is a known unicast address.
Which switching method has the lowest level of latency?
Cut-through
Store-and-forward
Fragment-free
Fast-forward
Which two commands can be used on a Windows host to display the routing table? (Choose two.)
Netstat -s
Route print
Show ip route
Netstat -r
Tracert
Which two functions are primary functions of a router? (Choose two.)
Packet forwarding
Microsegmentation
Domain name resolution
Path selection
Flow control
What is the binary representation of 0xCA?
10111010
11010101
11001010
11011010
At a minimum, which address is required on IPv6-enabled interfaces?
Link-local
Unique local
Site local
Global unicast
Which service provides dynamic global IPv6 addressing to end devices without using a server that keeps a record of available IPv6 addresses?
Stateful DHCPv6
SLAAC
Static IPv6 addressing
Stateless DHCPv6
What is the purpose of the command ping ::1?
It tests the internal configuration of an IPv6 host.
It tests the broadcast capability of all hosts on the subnet.
It tests the multicast connectivity to all hosts on the subnet.
It tests the reachability of the default gateway for the network.
How many usable IP addresses are available on the 192.168.1.0/27 network?
256
254
62
30
16
32
What is the process of dividing a data stream into smaller pieces before transmission?
Segmentation
Encapsulation
Encoding
Flow control
{"name":"Testing Quiz Part 2", "url":"https://www.quiz-maker.com/QPREVIEW","txt":"What subnet mask is needed if an IPv4 network has 40 devices that need IP addresses and address space is not to be wasted?, What are two characteristics shared by TCP and UDP? (Choose two.), Why are port numbers included in the TCP header of a segment?","img":"https://cdn.poll-maker.com/23-904082/i245561v1n1-245561.jpg?sz=1200"}