Network exam PART 1

Network Exam Part 1
Test your networking knowledge with this comprehensive quiz designed for networking professionals and enthusiasts alike. Dive into various topics including IPv6, TCP/UDP protocols, wireless networking, and network security.
This quiz offers:
- 30 multiple choice and checkbox questions
- Clear explanations for each answer
- Great preparation for networking certifications
A new network administrator has been asked to enter a banner message on a Cisco device. What is the fastest way a network administrator could test whether the banner is properly configured?
Enter CTRL-Z at the privileged mode prompt.
Power cycle the device.
Exit privileged EXEC mode and press Enter.
Exit global configuration mode.
Reboot the device
What happens when the transport input ssh command is entered on the switch vty lines?
The switch requires a username/password combination for remote access.
The SSH client on the switch is enabled.
Communication between the switch and remote users is encrypted.
The switch requires remote connections via a proprietary client software.
What is the subnet ID associated with the IPv6 address 2001:DA48:FC5:A4:3D1B::1/64?
2001:DA48::/64
2001::/64
2001:DA48:FC5:A4::/64
2001:DA48:FC5::A4:/64
A client is using SLAAC to obtain an IPv6 address for its interface. After an address has been generated and applied to the interface, what must the client do before it can begin to use this IPv6 address?
It must send an ICMPv6 Router Solicitation message to determine what default gateway it should use.
It must send a DHCPv6 INFORMATION-REQUEST message to request the address of the DNS server.
It must send a DHCPv6 REQUEST message to the DHCPv6 server to request permission to use this address.
It must send an ICMPv6 Neighbor Solicitation message to ensure that the address is not already in use on the network.
Which range of link-local addresses can be assigned to an IPv6-enabled interface?
FE80::/10
FDEE::/7
FF00::/8
FEC0::/10
What mechanism is used by a router to prevent a received IPv4 packet from traveling endlessly on a network?
It checks the value of the TTL field and if it is 100, it discards the packet and sends a Destination Unreachable message to the source host.
It increments the value of the TTL field by 1 and if the result is 100, it discards the packet and sends a Parameter Problem message to the source host.
It checks the value of the TTL field and if it is 0, it discards the packet and sends a Destination Unreachable message to the source host.
It decrements the value of the TTL field by 1 and if the result is 0, it discards the packet and sends a Time Exceeded message to the source host.
A network administrator is designing the layout of a new wireless network. Which three areas of concern should be accounted for when building a wireless network? (Choose three.)
Mobility options
Security
Interference
Coverage area
Packet collision
Extensive cabling
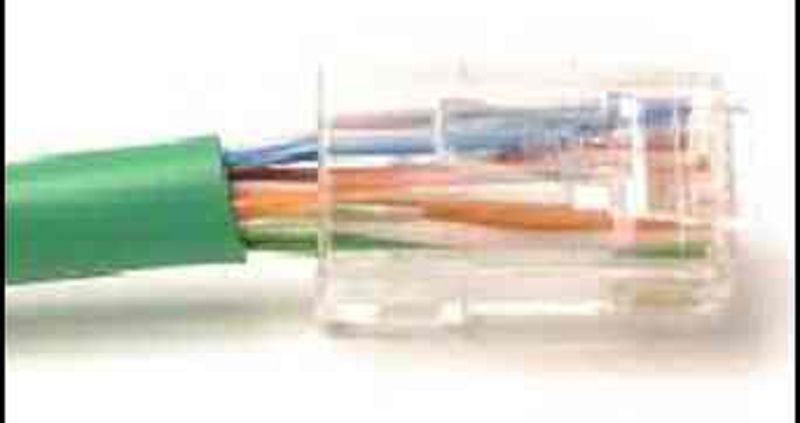
Refer to the exhibit. What is wrong with the displayed termination?
The untwisted length of each wire is too long.
The woven copper braid should not have been removed.
The wrong type of connector is being used.
The wires are too thick for the connector that is used.
A network administrator notices that some newly installed Ethernet cabling is carrying corrupt and distorted data signals. The new cabling was installed in the ceiling close to fluorescent lights and electrical equipment. Which two factors may interfere with the copper cabling and result in signal distortion and data corruption? (Choose two.)
EMI
Signal attenuation
Crosstalk
RFI
Extended length of cabling
Data is being sent from a source PC to a destination server. Which three statements correctly describe the function of TCP or UDP in this situation? (Choose three.)
TCP is the preferred protocol when a function requires lower network overhead.
The source port field identifies the running application or service that will handle data returning to the PC.
The TCP source port number identifies the sending host on the network.
UDP segments are encapsulated within IP packets for transport across the network.
The UDP destination port number identifies the application or service on the server which will handle the data.
The TCP process running on the PC randomly selects the destination port when establishing a session with the server.
A group of Windows PCs in a new subnet has been added to an Ethernet network. When testing the connectivity, a technician finds that these PCs can access local network resources but not the Internet resources. To troubleshoot the problem, the technician wants to initially confirm the IP address and DNS configurations on the PCs, and also verify connectivity to the local router. Which three Windows CLI commands and utilities will provide the necessary information? (Choose three.)
Netsh interface ipv6 show neighbor
Arp -a
Tracert
Ping
Ipconfig
Nslookup
Telnet
What two pieces of information are displayed in the output of the show ip interface brief command? (Choose two.)
Speed and duplex settings
MAC addresses
Next-hop addresses
Interface descriptions
IP addresses
Layer 1 statuses
A network administrator is adding a new LAN to a branch office. The new LAN must support 25 connected devices. What is the smallest network mask that the network administrator can use for the new network?
255.255.255.224
255.255.255.192
255.255.255.240
255.255.255.128
Which frame field is created by a source node and used by a destination node to ensure that a transmitted data signal has not been altered by interference, distortion, or signal loss?
Transport layer error check field
Error correction process field
Flow control field
User Datagram Protocol field
Frame check sequence field
What is a function of the data link layer?
Provides delivery of data between two applications
Provides for the exchange of frames over a common local media
Provides end-to-end delivery of data between hosts
Provides the formatting of data
What are three characteristics of the CSMA/CD process? (Choose three.)
After detecting a collision, hosts can attempt to resume transmission after a random time delay has expired.
A jam signal indicates that the collision has cleared and the media is not busy.
All of the devices on a segment see data that passes on the network medium.
The device with the electronic token is the only one that can transmit after a collision.
Devices can be configured with a higher transmission priority.
A device listens and waits until the media is not busy before transmitting.
What characteristic describes a Trojan horse?
An attack that slows or crashes a device or network service
Malicious software or code running on an end device
A network device that filters access and traffic coming into a network
The use of stolen credentials to access private data
What three requirements are defined by the protocols used in network communcations to allow message transmission across a network? (Choose three.)
End-device installation
Media selection
Message encoding
Delivery options
Connector specifications
Message size
What are two features of ARP? (Choose two.)
If a device receiving an ARP request has the destination IPv4 address, it responds with an ARP reply.
When a host is encapsulating a packet into a frame, it refers to the MAC address table to determine the mapping of IP addresses to MAC addresses.
If no device responds to the ARP request, then the originating node will broadcast the data packet to all devices on the network segment.
An ARP request is sent to all devices on the Ethernet LAN and contains the IP address of the destination host and its multicast MAC address.
If a host is ready to send a packet to a local destination device and it has the IP address but not the MAC address of the destination, it generates an ARP broadcast.
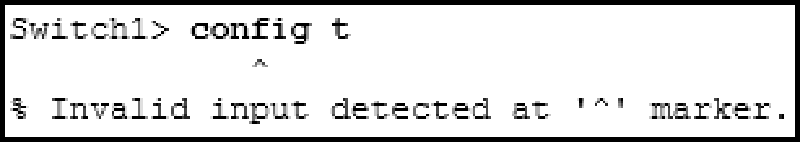
Refer to the exhibit. An administrator is trying to configure the switch but receives the error message that is displayed in the exhibit. What is the problem?
The entire command, configure terminal , must be used.
The administrator must connect via the console port to access global configuration mode.
The administrator is already in global configuration mode.
The administrator must first enter privileged EXEC mode before issuing the command.
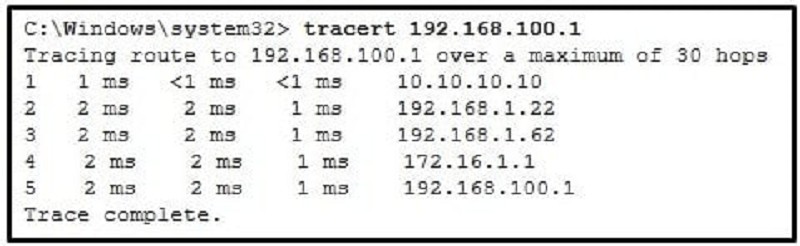
Refer to the exhibit. On the basis of the output, which two statements about network connectivity are correct? (Choose two.)
This host does not have a default gateway configured.
There are 4 hops between this device and the device at 192.168.100.1.
The average transmission time between the two hosts is 2 milliseconds.
There is connectivity between this device and the device at 192.168.100.1.
The connectivity between these two hosts allows for videoconferencing calls.
What are two characteristics of IP? (Choose two.)
Retransmits packets if errors occur
Guarantees delivery of packets
Does not require a dedicated end-to-end connection
Operates independently of the network media
Re-assembles out of order packets into the correct order at the receiver end
What will happen if the default gateway address is incorrectly configured on a host?
The host cannot communicate with hosts in other networks.
The host cannot communicate with other hosts in the local network.
A ping from the host to 127.0.0.1 would not be successful.
The switch will not forward packets initiated by the host.
The host will have to use ARP to determine the correct address of the default gateway.
Users report that the network access is slow. After questioning the employees, the network administrator learned that one employee downloaded a third-party scanning program for the printer. What type of malware might be introduced that causes slow performance of the network?
Spam
Virus
Worm
Phishing
A company has a file server that shares a folder named Public. The network security policy specifies that the Public folder is assigned Read-Only rights to anyone who can log into the server while the Edit rights are assigned only to the network admin group. Which component is addressed in the AAA network service framework?
Automation
Authorization
Accounting
Authentication
What are two common causes of signal degradation when using UTP cabling? (Choose two.)
Loss of light over long distances
Low-quality cable or connectors
Low-quality shielding in cable
Installing cables in conduit
Improper termination
Which scenario describes a function provided by the transport layer?
A student has two web browser windows open in order to access two web sites. The transport layer ensures the correct web page is delivered to the correct browser window.
A student is using a classroom VoIP phone to call home. The unique identifier burned into the phone is a transport layer address used to contact another network device on the same network.
A corporate worker is accessing a web server located on a corporate network. The transport layer formats the screen so the web page appears properly no matter what device is being used to view the web site.
A student is playing a short web-based movie with sound. The movie and sound are encoded within the transport layer header.
What is the consequence of configuring a router with the ipv6 unicast-routing global configuration command?
�Each router interface will generate an IPv6 link-local address.
The IPv6 enabled router interfaces begin sending ICMPv6 Router Advertisement messages.
It statically creates a global unicast address on this router.
All router interfaces will be automatically activated.
{"name":"Network exam PART 1", "url":"https://www.quiz-maker.com/QPREVIEW","txt":"Test your networking knowledge with this comprehensive quiz designed for networking professionals and enthusiasts alike. Dive into various topics including IPv6, TCP\/UDP protocols, wireless networking, and network security.This quiz offers:30 multiple choice and checkbox questionsClear explanations for each answerGreat preparation for networking certifications","img":"https:/images/course1.png"}