Final CCNA2

Final CCNA2 Quiz
Test your networking knowledge with our comprehensive Final CCNA2 Quiz. This quiz features 30 questions dedicated to key concepts in Cisco Certified Network Associate (CCNA) Level 2 topics including VLANs, routing protocols, security configurations, and wireless networking.
Whether you're preparing for an exam or looking to brush up on your skills, this quiz is a perfect way to enhance your understanding of networking fundamentals.
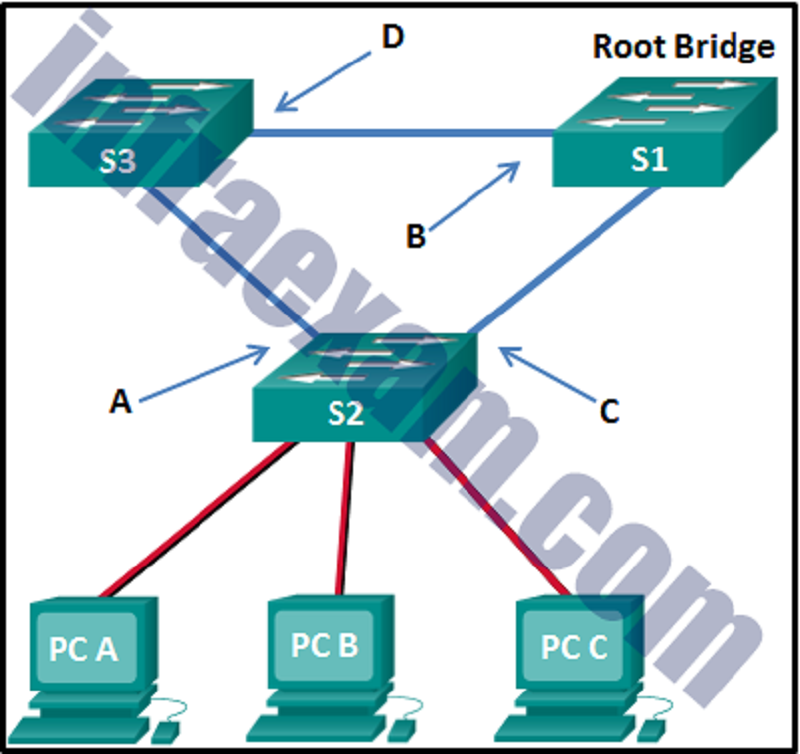
Refer to the exhibit. What are the possible port roles for ports A, B, C, and D in this RSTP-enabled network?
Designated, alternate, root, root
Designated, root, alternate, root
Alternate, root, designated, root
Alternate, designated, root, root
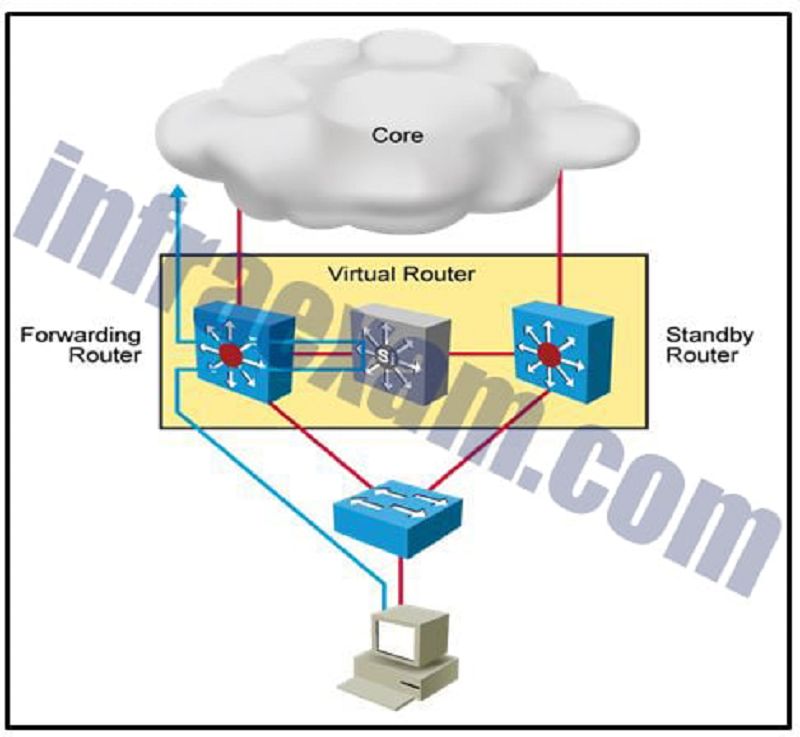
Refer to the exhibit. Which destination MAC address is used when frames are sent from the workstation to the default gateway?
MAC address of the virtual router
MAC addresses of both the forwarding and standby routers
MAC address of the standby router
MAC address of the forwarding router
What is a secure configuration option for remote access to a network device?
Configure SSH.
Configure 802.1x.
Configure an ACL and apply it to the VTY lines.
Configure Telnet.
After a host has generated an IPv6 address by using the DHCPv6 or SLAAC process, how does the host verify that the address is unique and therefore usable?
The host checks the local neighbor cache for the learned address and if the address is not cached, it it considered unique.
The host sends an ICMPv6 neighbor solicitation message to the DHCP or SLAAC-learned address and if no neighbor advertisement is returned, the address is considered unique.
The host sends an ICMPv6 echo request message to the DHCPv6 or SLAAC-learned address and if no reply is returned, the address is considered unique.
The host sends an ARP broadcast to the local link and if no hosts send a reply, the address is considered unique.
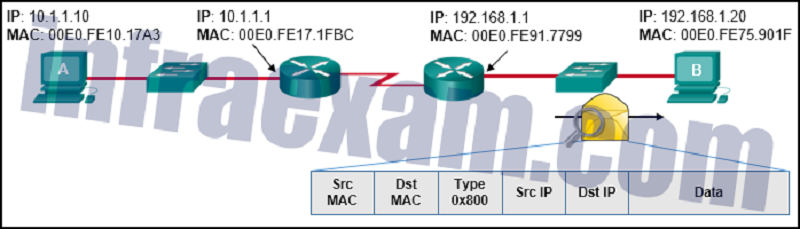
Refer to the exhibit. Host A has sent a packet to host B. What will be the source MAC and IP addresses on the packet when it arrives at host B?
Source MAC: 00E0.FE91.7799 Source IP: 10.1.1.10
Source MAC: 00E0.FE91.7799 Source IP: 10.1.1.1
Source MAC: 00E0.FE10.17A3 Source IP: 10.1.1.10
Source MAC: 00E0.FE10.17A3 Source IP: 192.168.1.1
Source MAC: 00E0.FE91.7799 Source IP: 192.168.1.1
After attaching four PCs to the switch ports, configuring the SSID and setting authentication properties for a small office network, a technician successfully tests the connectivity of all PCs that are connected to the switch and WLAN. A firewall is then configured on the device prior to connecting it to the Internet. What type of network device includes all of the described features?
Standalone wireless access point
Firewall appliance
Switch
Wireless router
Which wireless encryption method is the most secure?
WPA2 with AES
WPA2 with TKIP
WEP
WPA
Refer to the exhibit. A network administrator has connected two switches together using EtherChannel technology. If STP is running, what will be the end result?
The switches will load balance and utilize both EtherChannels to forward packets.
Both port channels will shutdown.
The resulting loop will create a broadcast storm.
STP will block one of the redundant links.
What are three techniques for mitigating VLAN attacks? (Choose three.)
Enable BPDU guard.
Set the native VLAN to an unused VLAN.
Use private VLANs.
Disable DTP.
Enable Source Guard.
Enable trunking manually.
An administrator is trying to remove configurations from a switch. After using the command erase startup-config and reloading the switch, the administrator finds that VLANs 10 and 100 still exist on the switch. Why were these VLANs not removed?
These VLANs cannot be deleted unless the switch is in VTP client mode.
These VLANs can only be removed from the switch by using the no vlan 10 and no vlan 100 commands.
These VLANs are default VLANs that cannot be removed.
Because these VLANs are stored in a file that is called vlan.dat that is located in flash memory, this file must be manually deleted.

Refer to the exhibit. Which static route would an IT technician enter to create a backup route to the 172.16.1.0 network that is only used if the primary RIP learned route fails?
Ip route 172.16.1.0 255.255.255.0 s0/0/0
Ip route 172.16.1.0 255.255.255.0 s0/0/0 91
Ip route 172.16.1.0 255.255.255.0 s0/0/0 111
Ip route 172.16.1.0 255.255.255.0 s0/0/0 121

Refer to the exhibit. In addition to static routes directing traffic to networks 10.10.0.0/16 and 10.20.0.0/16, Router HQ is also configured with the following command: ip route 0.0.0.0 0.0.0.0 serial 0/1/1 What is the purpose of this command?
Packets from the 10.10.0.0/16 network will be forwarded to network 10.20.0.0/16, and packets from the 10.20.0.0/16 network will be forwarded to network 10.10.0.0/16.
Packets that are received from the Internet will be forwarded to one of the LANs connected to R1 or R2.
Packets with a destination network that is not 10.10.0.0/16 or is not 10.20.0.0/16 or is not a directly connected network will be forwarded to the Internet.
Packets that are destined for networks that are not in the routing table of HQ will be dropped.
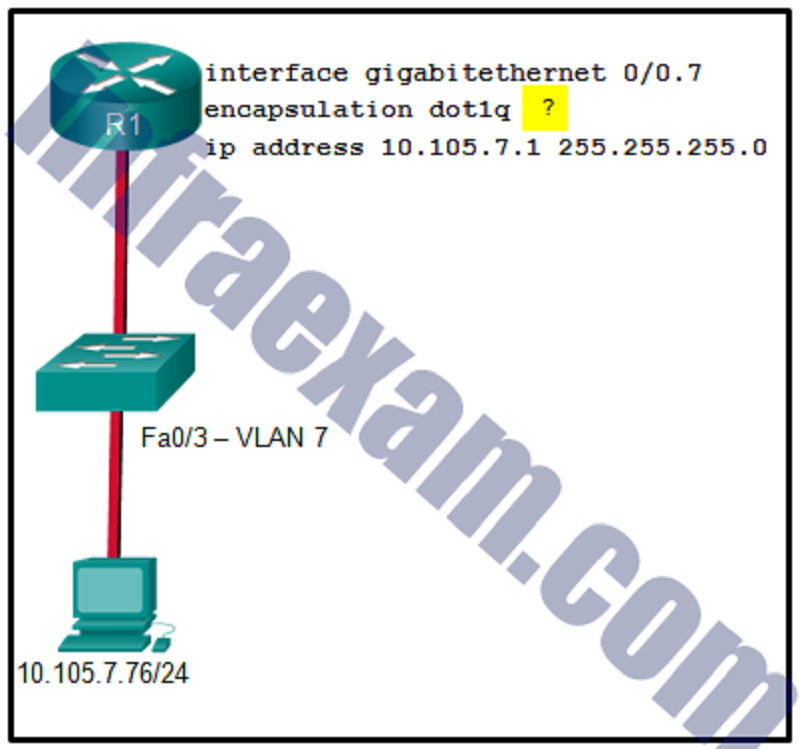
Refer to the exhibit. A network administrator is configuring inter-VLAN routing on a network. For now, only one VLAN is being used, but more will be added soon. What is the missing parameter that is shown as the highlighted question mark in the graphic?
It identifies the number of hosts that are allowed on the interface.
It identifies the type of encapsulation that is used.
It identifies the subinterface.
It identifies the native VLAN number.
It identifies the VLAN number.
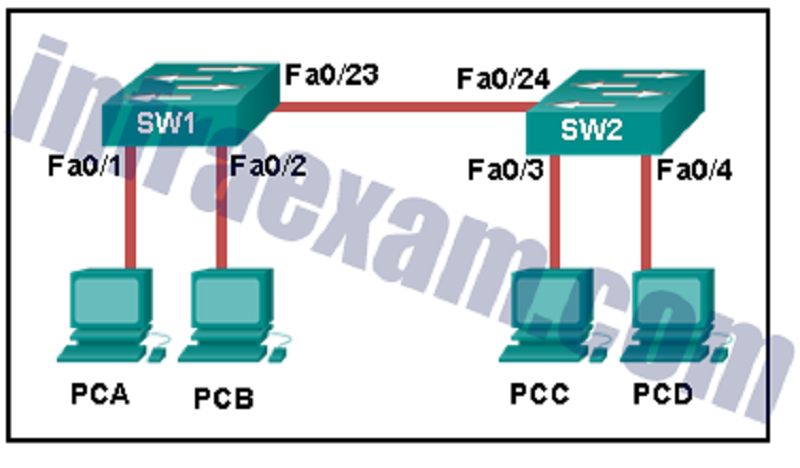
Refer to the exhibit. How is a frame sent from PCA forwarded to PCC if the MAC address table on switch SW1 is empty?
SW1 forwards the frame directly to SW2. SW2 floods the frame to all ports connected to SW2, excluding the port through which the frame entered the switch.
SW1 floods the frame on all ports on the switch, excluding the interconnected port to switch SW2 and the port through which the frame entered the switch.
SW1 drops the frame because it does not know the destination MAC address.
SW1 floods the frame on all ports on SW1, excluding the port through which the frame entered the switch.
A network administrator is configuring a WLAN. Why would the administrator disable the broadcast feature for the SSID?
To reduce the risk of interference by external devices such as microwave ovens
To reduce the risk of unauthorized APs being added to the network
To provide privacy and integrity to wireless traffic by using encryption
To eliminate outsiders scanning for available SSIDs in the area
Compared with dynamic routes, what are two advantages of using static routes on a router? (Choose two.)
They automatically switch the path to the destination network when the topology changes.
They improve the efficiency of discovering neighboring networks.
They use fewer router resources.
They improve network security.
They take less time to converge when the network topology changes.
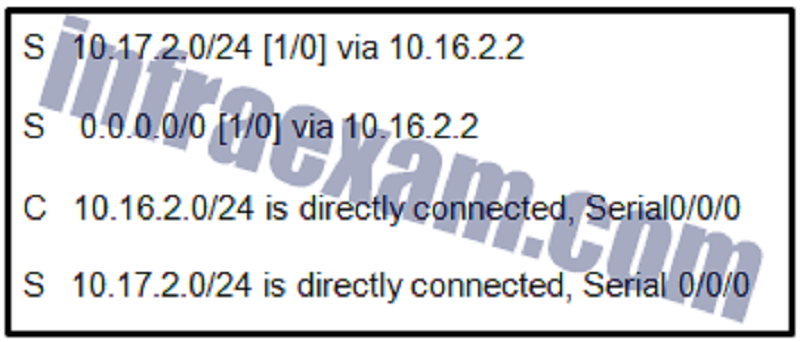
Refer to the exhibit. Which route was configured as a static route to a specific network using the next-hop address?
S 0.0.0.0/0 [1/0] via 10.16.2.2
S 10.17.2.0/24 is directly connected, Serial 0/0/0
C 10.16.2.0/24 is directly connected, Serial0/0/0
S 10.17.2.0/24 [1/0] via 10.16.2.2
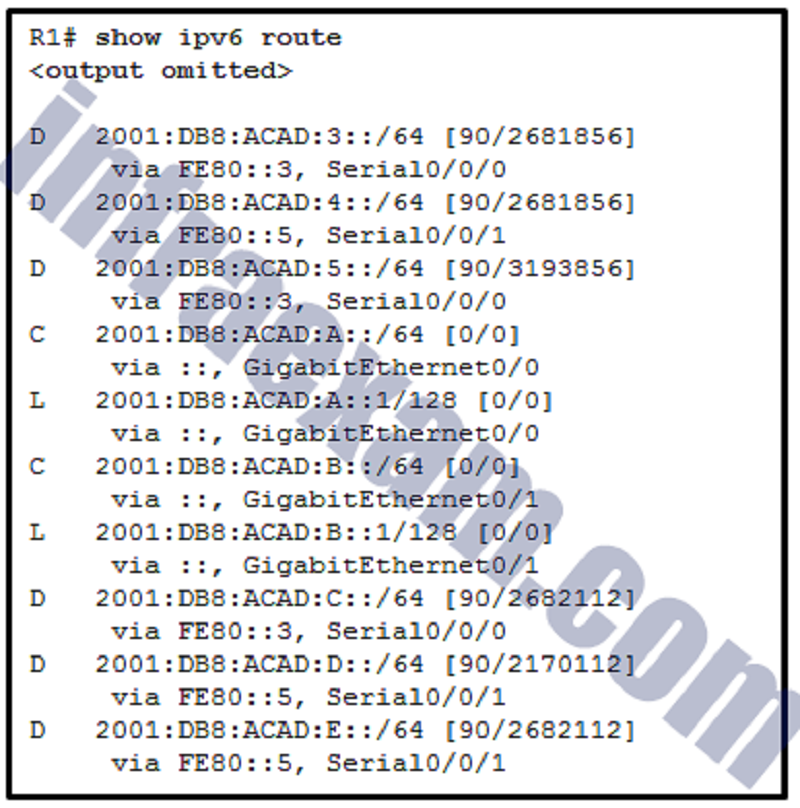
Refer to the exhibit. What is the metric to forward a data packet with the IPv6 destination address 2001:DB8:ACAD:E:240:BFF:FED4:9DD2?
90
128
2170112
2681856
2682112
3193856
A static route has been configured on a router. However, the destination network no longer exists. What should an administrator do to remove the static route from the routing table?
Remove the route using the no ip route command.
Change the administrative distance for that route.
Nothing. The static route will go away on its own.
Change the routing metric for that route.
Which two statements are characteristics of routed ports on a multilayer switch? (Choose two.)
In a switched network, they are mostly configured between switches at the core and distribution layers.
They are used for point-to-multipoint links.
They are not associated with a particular VLAN.
They support subinterfaces, like interfaces on the Cisco IOS routers.
The interface vlan command has to be entered to create a VLAN on routed ports.
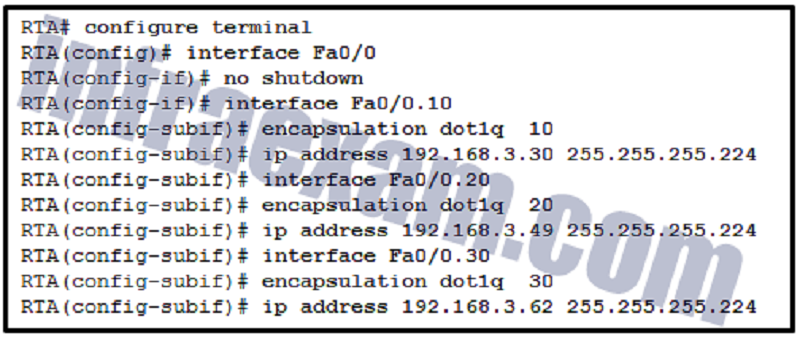
Refer to the exhibit. After attempting to enter the configuration that is shown in router RTA, an administrator receives an error and users on VLAN 20 report that they are unable to reach users on VLAN 30. What is causing the problem?
The no shutdown command should have been issued on Fa0/0.20 and Fa0/0.30.
There is no address on Fa0/0 to use as a default gateway.
Dot1q does not support subinterfaces.
RTA is using the same subnet for VLAN 20 and VLAN 30.

Refer to the exhibit. Which trunk link will not forward any traffic after the root bridge election process is complete?
Trunk1
Trunk2
Trunk3
Trunk4
A network administrator is preparing the implementation of Rapid PVST+ on a production network. How are the Rapid PVST+ link types determined on the switch interfaces?
Link types can only be determined if PortFast has been configured.
Link types can only be configured on access ports configured with a single VLAN.
Link types are determined automatically.
Link types must be configured with specific port configuration commands.
Which two types of spanning tree protocols can cause suboptimal traffic flows because they assume only one spanning-tree instance for the entire bridged network? (Choose two.)
STP
Rapid PVST+
MSTP
PVST+
RSTP
What action takes place when the source MAC address of a frame entering a switch appears in the MAC address table associated with a different port?
The switch purges the entire MAC address table.
The switch replaces the old entry and uses the more current port.
The switch updates the refresh timer for the entry.
The switch forwards the frame out of the specified port.
A network administrator configures the port security feature on a switch. The security policy specifies that each access port should allow up to two MAC addresses. When the maximum number of MAC addresses is reached, a frame with the unknown source MAC address is dropped and a notification is sent to the syslog server. Which security violation mode should be configured for each access port?
Warning
Restrict
Shutdown
Protect
Which network attack is mitigated by enabling BPDU guard?
Rogue switches on a network
Rogue DHCP servers on a network
MAC address spoofing
CAM table overflow attacks
A network administrator uses the spanning-tree portfast bpduguard default global configuration command to enable BPDU guard on a switch. However, BPDU guard is not activated on all access ports. What is the cause of the issue?
PortFast is not configured on all access ports.
Access ports belong to different VLANs.
BPDU guard needs to be activated in the interface configuration command mode.
Access ports configured with root guard cannot be configured with BPDU guard.
A new Layer 3 switch is connected to a router and is being configured for interVLAN routing. What are three of the five steps required for the configuration? (Choose three.) *
Creating SVI interfaces
Creating VLANs
Installing a static route
Adjusting the route metric
Implementing a routing protocol
Modifying the default VLAN
Assigning ports to VLANs
A company is deploying a wireless network in the distribution facility in a Boston suburb. The warehouse is quite large and it requires multiple access points to be used. Because some of the company devices still operate at 2.4GHz, the network administrator decides to deploy the 802.11g standard. Which channel assignments on the multiple access points will make sure that the wireless channels are not overlapping?
Channels 1, 6, and 11
Channels 2, 6, and 10
Channels 1, 5, and 9
Channels 1, 7, and 13
What method of wireless authentication is dependent on a RADIUS authentication server?
WEP
WPA2 Enterprise
WPA Personal
WPA2 Personal
An administrator notices that large numbers of packets are being dropped on one of the branch routers. What should be done or checked?
Create extra static routes to the same location with an AD of 1.
Check the routing table for a missing static route.
Create static routes to all internal networks and a default route to the internet.
Check the statistics on the default route for oversaturation.
In which situation would a technician use the show interfaces switch command?
To determine if remote access is enabled
When an end device can reach local devices, but not remote devices
To determine the MAC address of a directly attached network device on a particular interface
When packets are being dropped from a particular directly attached host
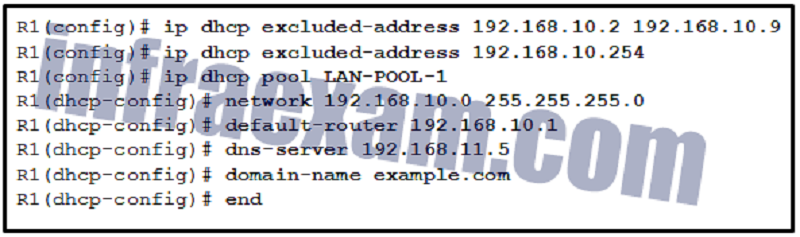
Refer to the exhibit. If the IP addresses of the default gateway router and the DNS server are correct, what is the configuration problem?
The default-router and dns-server commands need to be configured with subnet masks.
The DNS server and the default gateway router should be in the same subnet.
The IP address of the DNS server is not contained in the excluded address list.
The IP address of the default gateway router is not contained in the excluded address list.
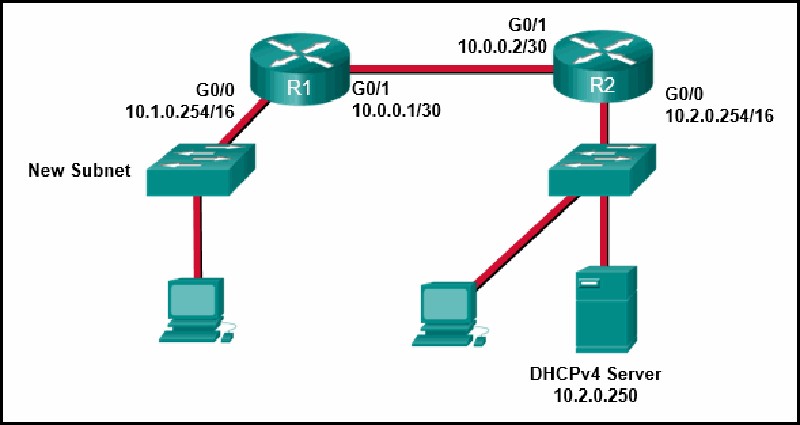
Refer to the exhibit. A network administrator has added a new subnet to the network and needs hosts on that subnet to receive IPv4 addresses from the DHCPv4 server. What two commands will allow hosts on the new subnet to receive addresses from the DHCP4 server? (Choose two.)
R2(config-if)# ip helper-address 10.2.0.250
R1(config)# interface G0/1
R1(config-if)# ip helper-address 10.2.0.250
R1(config)# interface G0/0
R1(config-if)# ip helper-address 10.1.0.254
R2(config)# interface G0/0

Refer to the exhibit. R1 has been configured as shown. However, PC1 is not able to receive an IPv4 address. What is the problem?
R1 is not configured as a DHCPv4 server.
A DHCP server must be installed on the same LAN as the host that is receiving the IP address.
The ip helper-address command was applied on the wrong interface.
The ip address dhcp command was not issued on the interface Gi0/1.
What network attack seeks to create a DoS for clients by preventing them from being able to obtain a DHCP lease?
CAM table attack
IP address spoofing
DHCP spoofing
DHCP starvation
A cybersecurity analyst is using the macof tool to evaluate configurations of switches deployed in the backbone network of an organization. Which type of LAN attack is the analyst targeting during this evaluation?
VLAN double-tagging
MAC address table overflow
VLAN hopping
DHCP spoofing
Which information does a switch use to populate the MAC address table?
The source MAC address and the incoming port
The destination MAC address and the incoming port
The source MAC address and the outgoing port
The source and destination MAC addresses and the outgoing port
The source and destination MAC addresses and the incoming port
The destination MAC address and the outgoing port
Which statement describes a result after multiple Cisco LAN switches are interconnected?
There is one broadcast domain and one collision domain per switch.
The broadcast domain expands to all switches.
One collision domain exists per switch.
Frame collisions increase on the segments connecting the switches.
Which method of IPv6 prefix assignment relies on the prefix contained in RA messages?
EUI-64
Stateful DHCPv6
Static
SLAAC
On a Cisco 3504 WLC Summary page ( Advanced > Summary ), which tab allows a network administrator to configure a particular WLAN with a WPA2 policy?
MANAGEMENT
WLANs
SECURITY
WIRELESS
A network administrator of a small advertising company is configuring WLAN security by using the WPA2 PSK method. Which credential do office users need in order to connect their laptops to the WLAN?
A key that matches the key on the AP
A username and password configured on the AP
A user passphrase
The company username and password through Active Directory service

What two default wireless router settings can affect network security? (Choose two.)
The SSID is broadcast.
MAC address filtering is enabled.
WEP encryption is enabled.
The wireless channel is automatically selected.
A well-known administrator password is set.
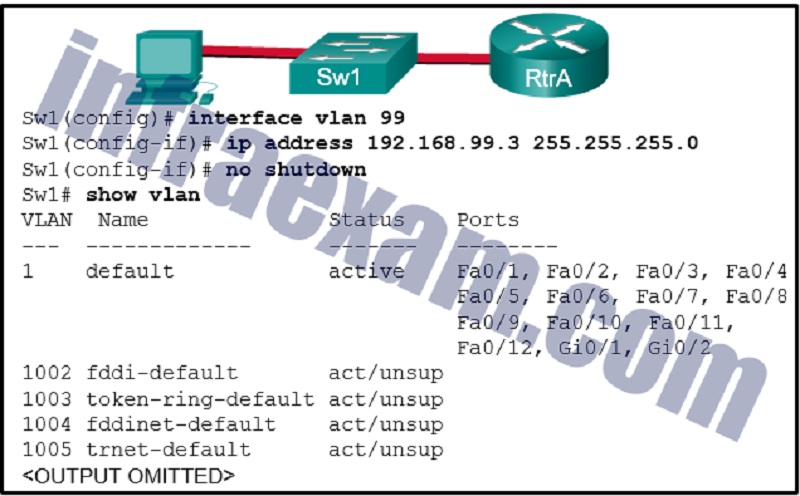
Refer to the exhibit. Based on the exhibited configuration and output, why is VLAN 99 missing?
Because there is a cabling problem on VLAN 99
Because VLAN 1 is up and there can only be one management VLAN on the switch
Because VLAN 99 has not yet been created
Because VLAN 99 is not a valid management VLAN
Which three pairs of trunking modes will establish a functional trunk link between two Cisco switches? (Choose three.)
Access – trunk
Dynamic auto – dynamic auto
Dynamic desirable – dynamic desirable
Dynamic desirable – dynamic auto
Dynamic desirable – trunk
Access – dynamic auto
Which three steps should be taken before moving a Cisco switch to a new VTP management domain? (Choose three.)
Reset the VTP counters to allow the switch to synchronize with the other switches in the domain.
Download the VTP database from the VTP server in the new domain.
Select the correct VTP mode and version.
Reboot the switch.
Configure the VTP server in the domain to recognize the BID of the new switch.
Configure the switch with the name of the new management domain.
Select the three PAgP channel establishment modes. (Choose three.)
Active
Passive
Desirable
On
Auto
Blocking

Refer to the exhibit. Which static route command can be entered on R1 to forward traffic to the LAN connected to R2?
Ipv6 route 2001:db8:12:10::/64 S0/0/0 fe80::2
Ipv6 route 2001:db8:12:10::/64 S0/0/1 fe80::2
Ipv6 route 2001:db8:12:10::/64 S0/0/1 2001:db8:12:10::1
Ipv6 route 2001:db8:12:10::/64 S0/0/0
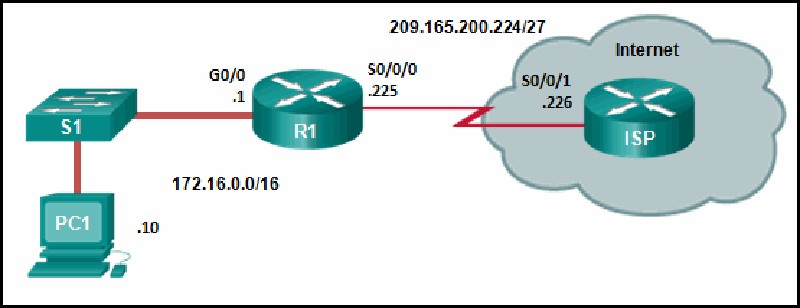
Refer to the exhibit. R1 was configured with the static route command ip route 209.165.200.224 255.255.255.224 S0/0/0 and consequently users on network 172.16.0.0/16 are unable to reach resources on the Internet. How should this static route be changed to allow user traffic from the LAN to reach the Internet?
Add the next-hop neighbor address of 209.165.200.226.
Change the destination network and mask to 0.0.0.0 0.0.0.0.
Change the exit interface to S0/0/1.
Add an administrative distance of 254.

Refer to the exhibit. Currently router R1 uses an EIGRP route learned from Branch2 to reach the 10.10.0.0/16 network. Which floating static route would create a backup route to the 10.10.0.0/16 network in the event that the link between R1 and Branch2 goes down?
Ip route 10.10.0.0 255.255.0.0 Serial 0/0/0 100
Ip route 10.10.0.0 255.255.0.0 209.165.200.226 100
Ip route 10.10.0.0 255.255.0.0 209.165.200.225 100
Ip route 10.10.0.0 255.255.0.0 209.165.200.225 50
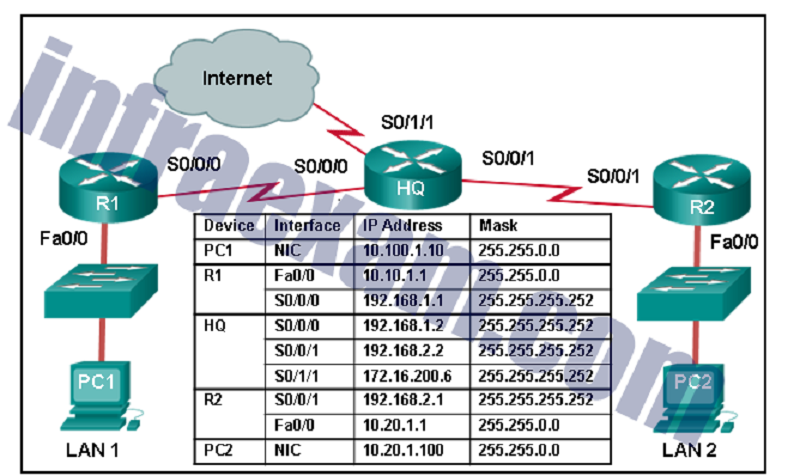
Refer to the exhibit. A network engineer is configuring IPv6 routing on the network. Which command issued on router HQ will configure a default route to the Internet to forward packets to an IPv6 destination network that is not listed in the routing table?
Ipv6 route ::/0 serial 0/1/1
Ipv6 route ::1/0 serial 0/1/1
Ipv6 route ::/0 serial 0/0/0
Ip route 0.0.0.0 0.0.0.0 serial 0/1/1
What protocol or technology uses a standby router to assume packet-forwarding responsibility if the active router fails?
HSRP
EtherChannel
VTP
DTP
What is the effect of entering the ip arp inspection vlan 10 configuration command on a switch?
It enables DHCP snooping globally on a switch.
It specifies the maximum number of L2 addresses allowed on a port.
It enables DAI on specific switch interfaces previously configured with DHCP snooping.
It globally enables BPDU guard on all PortFast-enabled ports.
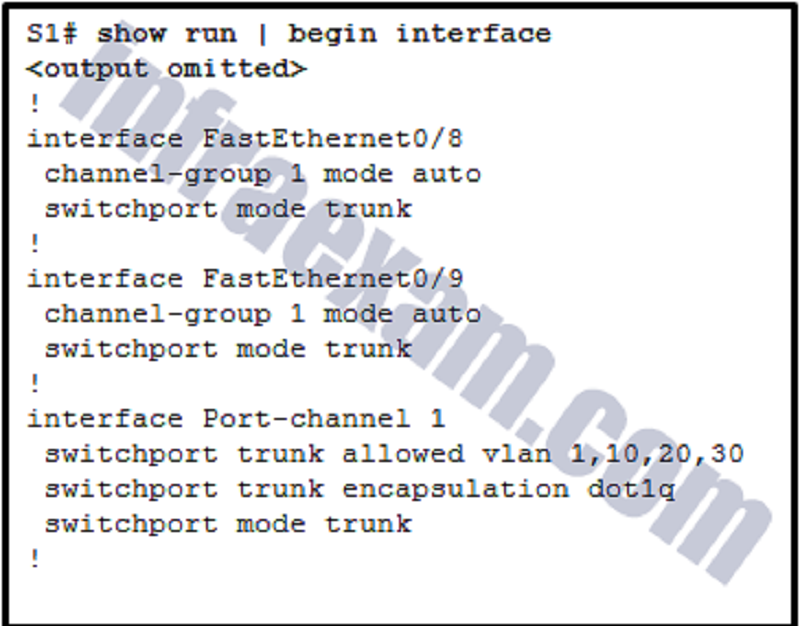
Refer to the exhibit. A network administrator is reviewing the configuration of switch S1. Which protocol has been implemented to group multiple physical ports into one logical link?
DTP
LACP
PAgP
STP
Successful inter-VLAN routing has been operating on a network with multiple VLANs across multiple switches for some time. When an inter-switch trunk link fails and Spanning Tree Protocol brings up a backup trunk link, it is reported that hosts on two VLANs can access some, but not all the network resources that could be accessed previously. Hosts on all other VLANS do not have this problem. What is the most likely cause of this problem?
The allowed VLANs on the backup link were not configured correctly.
The protected edge port function on the backup trunk interfaces has been disabled.
Dynamic Trunking Protocol on the link has failed.
Inter-VLAN routing also failed when the trunk link failed.

Refer to the exhibit. An administrator is attempting to install an IPv6 static route on router R1 to reach the network attached to router R2. After the static route command is entered, connectivity to the network is still failing. What error has been made in the static route configuration?
The interface is incorrect.
The next hop address is incorrect.
The network prefix is incorrect.
The destination network is incorrect.
What protocol or technology uses source IP to destination IP as a load-balancing mechanism?
EtherChannel
VTP
STP
DTP
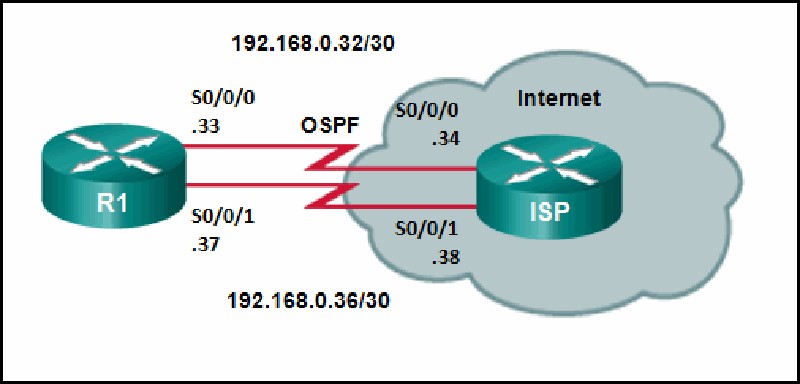
Refer to the exhibit. Router R1 has an OSPF neighbor relationship with the ISP router over the 192.168.0.32 network. The 192.168.0.36 network link should serve as a backup when the OSPF link goes down. The floating static route command ip route 0.0.0.0 0.0.0.0 S0/0/1 100 was issued on R1 and now traffic is using the backup link even when the OSPF link is up and functioning. Which change should be made to the static route command so that traffic will only use the OSPF link when it is up?
Change the administrative distance to 120.
Change the administrative distance to 1.
Add the next hop neighbor address of 192.168.0.36.
Change the destination network to 192.168.0.34.
Which type of static route is configured with a greater administrative distance to provide a backup route to a route learned from a dynamic routing protocol?
Standard static route
Default static route
Floating static route
Summary static route
Which option shows a correctly configured IPv4 default static route?
Ip route 0.0.0.0 0.0.0.0 S0/0/0
Ip route 0.0.0.0 255.0.0.0 S0/0/0
Ip route 0.0.0.0 255.255.255.0 S0/0/0
Ip route 0.0.0.0 255.255.255.255 S0/0/0
Which command will start the process to bundle two physical interfaces to create an EtherChannel group via LACP?
Channel-group 2 mode auto
Channel-group 1 mode desirable
Interface port-channel 2
Interface range GigabitEthernet 0/4 – 5
What would be the primary reason an attacker would launch a MAC address overflow attack?
So that the attacker can execute arbitrary code on the switch
So that the switch stops forwarding traffic
So that the attacker can see frames that are destined for other hosts
So that legitimate hosts cannot obtain a MAC address
What is a method to launch a VLAN hopping attack?
Introducing a rogue switch and enabling trunking
Flooding the switch with MAC addresses
Sending spoofed IP addresses from the attacking host
Sending spoofed native VLAN information
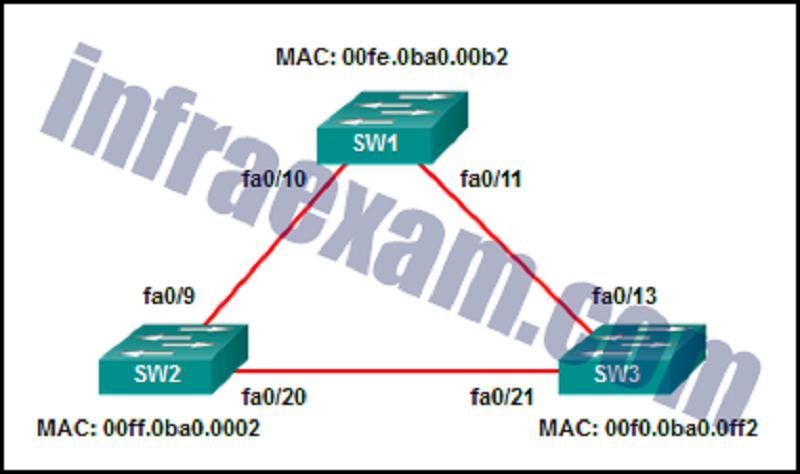
Refer to the exhibit. All the displayed switches are Cisco 2960 switches with the same default priority and operating at the same bandwidth. Which three ports will be STP designated ports? (Choose three.)
Fa0/21
Fa0/10
Fa0/13
Fa0/9
Fa0/20
Fa0/11
What is the common term given to SNMP log messages that are generated by network devices and sent to the SNMP server?
Traps
Auditing
Acknowledgments
Warnings
A technician is troubleshooting a slow WLAN and decides to use the split-the-traffic approach. Which two parameters would have to be configured to do this? (Choose two.)
Configure the 2.4 GHz band for basic internet traffic that is not time sensitive.
Configure the security mode to WPA Personal TKIP/AES for both networks.
Configure the security mode to WPA Personal TKIP/AES for one network and WPA2 Personal AES for the other network
Configure a common SSID for both split networks.
Configure the 5 GHz band for streaming multimedia and time sensitive traffic.
A company security policy requires that all MAC addressing be dynamically learned and added to both the MAC address table and the running configuration on each switch. Which port security configuration will accomplish this?
Auto secure MAC addresses
Dynamic secure MAC addresses
Static secure MAC addresses
Sticky secure MAC addresses
What is the IPv6 prefix that is used for link-local addresses?
FE80::/10
FF01::/8
FC00::/7
2001::/3
What action takes place when a frame entering a switch has a unicast destination MAC address that is not in the MAC address table?
The switch resets the refresh timer on all MAC address table entries.
The switch updates the refresh timer for the entry.
The switch replaces the old entry and uses the more current port.
The switch will forward the frame out all ports except the incoming port.
A new switch is to be added to an existing network in a remote office. The network administrator does not want the technicians in the remote office to be able to add new VLANs to the switch, but the switch should receive VLAN updates from the VTP domain. Which two steps must be performed to configure VTP on the new switch to meet these conditions? (Choose two.)
Configure the existing VTP domain name on the new switch.
Configure all ports of both switches to access mode.
Enable VTP pruning.
Configure an IP address on the new switch.
Configure the new switch as a VTP client.
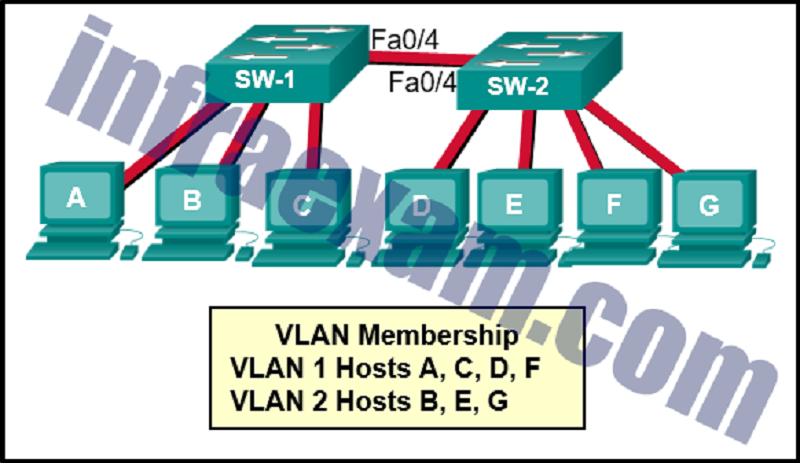
Refer to the exhibit. Which three hosts will receive ARP requests from host A, assuming that port Fa0/4 on both switches is configured to carry traffic for multiple VLANs? (Choose three.)
Host F
Host B
Host D
Host G
Host C
Host E
A technician is configuring a router for a small company with multiple WLANs and doesn’t need the complexity of a dynamic routing protocol. What should be done or checked?
Check the configuration on the floating static route and adjust the AD.
Create a floating static route to that network.
Verify that there is not a default route in any of the edge router routing tables.
Create static routes to all internal networks and a default route to the internet.
Which two functions are performed by a WLC when using split media access control (MAC)? (Choose two.)
Packet acknowledgments and retransmissions
Frame translation to other protocols
Association and re-association of roaming clients
Beacons and probe responses
Frame queuing and packet prioritization
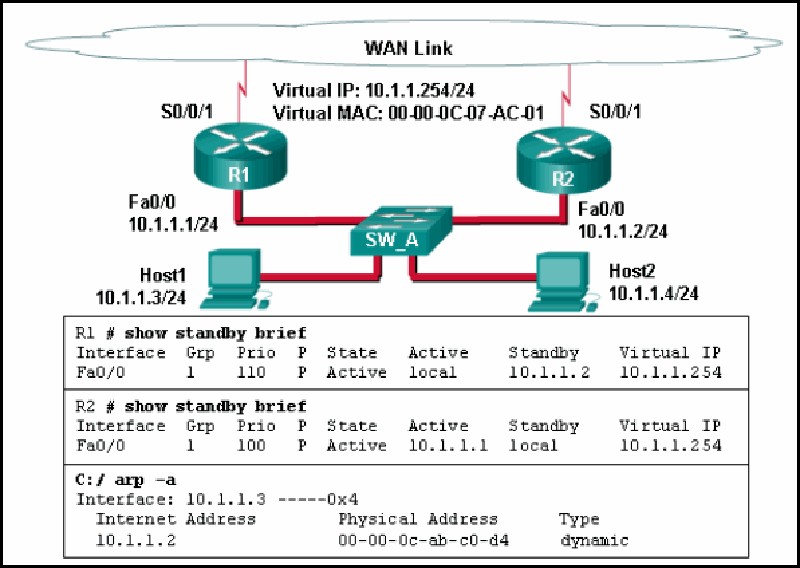
Refer to the exhibit. A network administrator configured routers R1 and R2 as part of HSRP group 1. After the routers have been reloaded, a user on Host1 complained of lack of connectivity to the Internet The network administrator issued the show standby brief command on both routers to verify the HSRP operations. In addition, the administrator observed the ARP table on Host1. Which entry should be seen in the ARP table on Host1 in order to gain connectivity to the Internet?
The IP address and the MAC address of R1
The virtual IP address of the HSRP group 1 and the MAC address of R1
The virtual IP address of the HSRP group 1 and the MAC address of R2
The virtual IP address and the virtual MAC address for the HSRP group 1
A network administrator is configuring a new Cisco switch for remote management access. Which three items must be configured on the switch for the task? (Choose three.)
IP address
Default gateway
Default VLAN
Vty lines
VTP domain
Loopback address
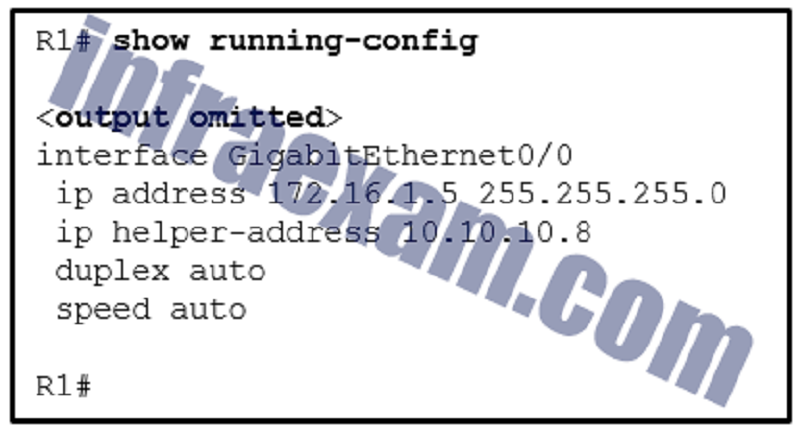
Refer to the exhibit. What can be concluded about the configuration shown on R1?
R1 is configured as a DHCPv4 relay agent.
R1 will send a message to a local DHCPv4 client to contact a DHCPv4 server at 10.10.10.8.
R1 will broadcast DHCPv4 requests on behalf of local DHCPv4 clients.
R1 is operating as a DHCPv4 server.
What action does a DHCPv4 client take if it receives more than one DHCPOFFER from multiple DHCP servers?
It sends a DHCPREQUEST that identifies which lease offer the client is accepting.
It sends a DHCPNAK and begins the DHCP process over again.
It accepts both DHCPOFFER messages and sends a DHCPACK.
It discards both offers and sends a new DHCPDISCOVER.
What protocol should be disabled to help mitigate VLAN attacks?
STP
CDP
DTP
ARP
Why is DHCP snooping required when using the Dynamic ARP Inspection feature?
It uses the MAC address table to verify the default gateway IP address.
It redirects ARP requests to the DHCP server for verification.
It relies on the settings of trusted and untrusted ports set by DHCP snooping.
It uses the MAC-address-to-IP-address binding database to validate an ARP packet.
To obtain an overview of the spanning tree status of a switched network, a network engineer issues the show spanning-tree command on a switch. Which two items of information will this command display? (Choose two.)
The role of the ports in all VLANs.
The root bridge BID.
The number of broadcasts received on each root port.
The IP address of the management VLAN interface.
The status of native VLAN ports.
A WLAN engineer deploys a WLC and five wireless APs using the CAPWAP protocol with the DTLS feature to secure the control plane of the network devices. While testing the wireless network, the WLAN engineer notices that data traffic is being exchanged between the WLC and the APs in plain-text and is not being encrypted. What is the most likely reason for this?
DTLS only provides data security through authentication and does not provide encryption for data moving between a wireless LAN controller (WLC) and an access point (AP).
Data encryption requires a DTLS license to be installed on each access point (AP) prior to being enabled on the wireless LAN controller (WLC).
Although DTLS is enabled by default to secure the CAPWAP control channel, it is disabled by default for the data channel.
DTLS is a protocol that only provides security between the access point (AP) and the wireless client.
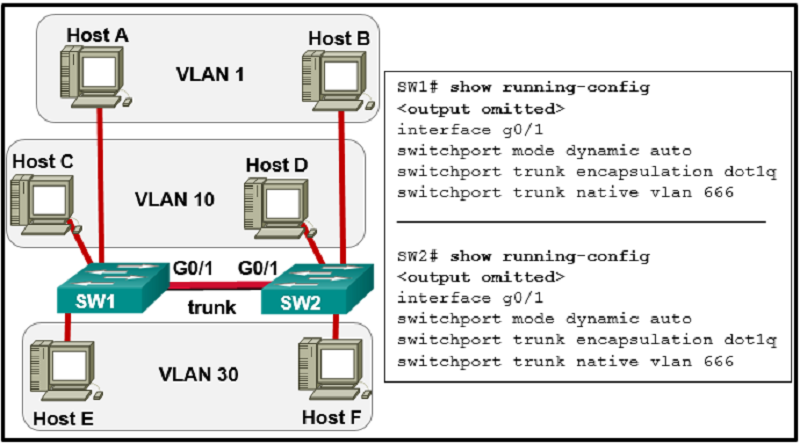
Refer to the exhibit. The network administrator configures both switches as displayed. However, host C is unable to ping host D and host E is unable to ping host F. What action should the administrator take to enable this communication?
Associate hosts A and B with VLAN 10 instead of VLAN 1.
Configure either trunk port in the dynamic desirable mode.
Add the switchport nonegotiate command to the configuration of SW2.
Include a router in the topology.
Remove the native VLAN from the trunk.
What action takes place when the source MAC address of a frame entering a switch is not in the MAC address table?
The switch replaces the old entry and uses the more current port.
The switch adds a MAC address table entry for the destination MAC address and the egress port.
The switch updates the refresh timer for the entry.
The switch adds the MAC address and incoming port number to the table.
A technician is configuring a wireless network for a small business using a SOHO wireless router. Which two authentication methods are used, if the router is configured with WPA2? (Choose two.) **
AES
TKIP
Personal
WEP
Enterprise
A network administrator is adding a new WLAN on a Cisco 3500 series WLC. Which tab should the administrator use to create a new VLAN interface to be used for the new WLAN?
WLANs
CONTROLLER
WIRELESS
MANAGEMENT
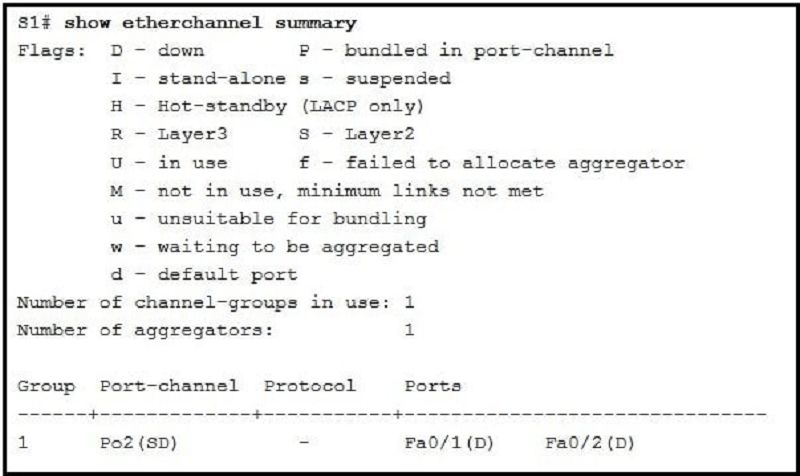
Refer to the exhibit. Which two conclusions can be drawn from the output? (Choose two.)
The port channel ID is 2.
The bundle is fully operational.
The port channel is a Layer 3 channel.
The load-balancing method used is source port to destination port.
The EtherChannel is down.
Which three statements accurately describe duplex and speed settings on Cisco 2960 switches? (Choose three.)
By default, the speed is set to 100 Mb/s and the duplex mode is set to autonegotiation.
An autonegotiation failure can result in connectivity issues.
The duplex and speed settings of each switch port can be manually configured.
When the speed is set to 1000 Mb/s, the switch ports will operate in full-duplex mode.
By default, the autonegotiation feature is disabled.
Enabling autonegotiation on a hub will prevent mismatched port speeds when connecting the hub to the switch.
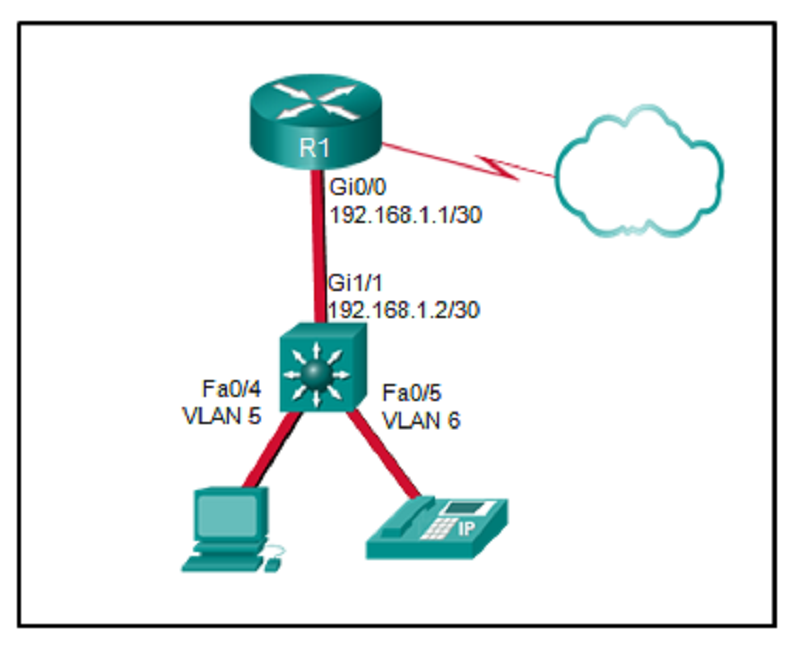
Refer to the exhibit. A Layer 3 switch routes for three VLANs and connects to a router for Internet connectivity. Which two configurations would be applied to the switch? (Choose two.)
(config)# interface fastethernet0/4 (config-if)# switchport mode trunk
(config)# interface vlan 1 (config-if)# ip address 192.168.1.2 255.255.255.0 (config-if)# no shutdown
(config)# ip routing
(config)# interface gigabitethernet 1/1 (config-if)# no switchport (config-if)# ip address 192.168.1.2 255.255.255.252
(config)# interface gigabitethernet1/1 (config-if)# switchport mode trunk

Refer to the exhibit. Consider that the main power has just been restored. PC3 issues a broadcast IPv4 DHCP request. To which port will SW1 forward this request?
To Fa0/1 only
To Fa0/1, Fa0/2, and Fa0/4 only
To Fa0/1, Fa0/2, Fa0/3, and Fa0/4
To Fa0/1, Fa0/2, and Fa0/3 only
To Fa0/1 and Fa0/2 only
Which statement is correct about how a Layer 2 switch determines how to forward frames?
Only frames with a broadcast destination address are forwarded out all active switch ports.
Frame forwarding decisions are based on MAC address and port mappings in the CAM table.
Cut-through frame forwarding ensures that invalid frames are always dropped.
Unicast frames are always forwarded regardless of the destination MAC address.
Employees are unable to connect to servers on one of the internal networks. What should be done or checked?
Use the “show ip interface brief” command to see if an interface is down.
Verify that there is not a default route in any of the edge router routing tables.
Check the statistics on the default route for oversaturation.
Create static routes to all internal networks and a default route to the internet.
What protocol or technology requires switches to be in server mode or client mode?
VTP
EtherChannel
HSRP
DTP
What is the effect of entering the shutdown configuration command on a switch?
It disables an unused port.
It enables portfast on a specific switch interface.
It disables DTP on a non-trunking interface.
It enables BPDU guard on a specific port.
What else is required when configuring an IPv6 static route using a next-hop link-local address? **
Network number and subnet mask on the interface of the neighbor router
Ip address of the neighbor router
Interface number and type
Administrative distance
A junior technician was adding a route to a LAN router. A traceroute to a device on the new network revealed a wrong path and unreachable status. What should be done or checked?
Verify that there is not a default route in any of the edge router routing tables.
Create a floating static route to that network.
Check the configuration on the floating static route and adjust the AD.
Check the configuration of the exit interface on the new static route.
A network engineer is troubleshooting a newly deployed wireless network that is using the latest 802.11 standards. When users access high bandwidth services such as streaming video, the wireless network performance is poor. To improve performance the network engineer decides to configure a 5 Ghz frequency band SSID and train users to use that SSID for streaming media services. Why might this solution improve the wireless network performance for that type of service?
The 5 GHz band has more channels and is less crowded than the 2.4 GHz band, which makes it more suited to streaming multimedia.
The only users that can switch to the 5 GHz band will be those with the latest wireless NICs, which will reduce usage.
Requiring the users to switch to the 5 GHz band for streaming media is inconvenient and will result in fewer users accessing these services.
The 5 GHz band has a greater range and is therefore likely to be interference-free.
On what switch ports should BPDU guard be enabled to enhance STP stability?
Only ports that are elected as designated ports
Only ports that attach to a neighboring switch
All PortFast-enabled ports
All trunk ports that are not root ports
How will a router handle static routing differently if Cisco Express Forwarding is disabled?
Serial point-to-point interfaces will require fully specified static routes to avoid routing inconsistencies.
It will not perform recursive lookups.
Static routes that use an exit interface will be unnecessary.
Ethernet multiaccess interfaces will require fully specified static routes to avoid routing inconsistencies.
What protocol or technology allows data to transmit over redundant switch links?
STP
VTP
EtherChannel
DTP
{"name":"Final CCNA2", "url":"https://www.quiz-maker.com/QPREVIEW","txt":"Test your networking knowledge with our comprehensive Final CCNA2 Quiz. This quiz features 30 questions dedicated to key concepts in Cisco Certified Network Associate (CCNA) Level 2 topics including VLANs, routing protocols, security configurations, and wireless networking.Whether you're preparing for an exam or looking to brush up on your skills, this quiz is a perfect way to enhance your understanding of networking fundamentals.","img":"https:/images/course1.png"}